One-Sentence Definition
Know Your Customer (KYC) is a regulated set of identity verification, risk assessment, and ongoing monitoring processes that financial institutions use to establish, validate, and continuously reassess the true identity and risk profile of a customer before and during a business relationship.

What Is Know Your Customer (KYC)?
Know Your Customer is not a single check, document, or onboarding step. It is a control framework embedded into financial operations that determines whether an institution can lawfully establish and maintain a relationship with an individual or entity. At its core, KYC answers three questions with evidentiary certainty: who the customer is, whether that identity is real and verifiable, and whether the customer presents an acceptable level of financial crime risk.
KYC operates across the full customer lifecycle. It begins before account opening, continues through transactional activity, and persists until the relationship ends. The framework combines identity proofing, data validation, risk classification, and periodic reassessment, all governed by jurisdiction-specific regulations and supervisory expectations.
KYC is therefore best understood as infrastructure, not paperwork. It connects onboarding systems, data sources, compliance rules, monitoring engines, and audit trails into a defensible decision system that regulators can inspect and institutions can rely upon.
What KYC Is NOT
KYC is frequently misunderstood because it is visible to users only at its most superficial layer. Clarifying what KYC is not is essential to avoiding conceptual errors.
KYC is not simple document collection. Uploading an ID card or utility bill is only an input. Without verification, validation, and risk interpretation, documents have no regulatory value.
KYC is not a one-time event. Passing identity checks at onboarding does not satisfy KYC obligations if customer behavior, ownership, or risk exposure later changes.
KYC is not identical to AML. Anti-Money Laundering programs are broader and include transaction monitoring, investigations, and reporting. KYC is a foundational pillar within AML, not a replacement for it.
KYC is not fraud prevention alone. While identity verification helps prevent fraud, KYC exists primarily to manage systemic financial crime risk, not just individual fraud losses.
KYC is not optional based on company size or technology stack. If an entity performs regulated financial activities, KYC obligations apply regardless of whether the institution is a bank, fintech, exchange, or payment intermediary.
Why KYC Exists
KYC exists because modern financial systems are anonymous by default while regulated finance cannot be. Money can move instantly, globally, and digitally, but regulators require accountability for who controls that money and how it is used.
The framework was institutionalized to address specific systemic failures. Anonymous accounts enabled money laundering, terrorist financing, sanctions evasion, tax evasion, and large-scale fraud. Without identity controls, financial institutions could not reliably distinguish legitimate customers from illicit actors.
KYC also exists to allocate liability. Regulators place the burden of customer verification on institutions because they are the gatekeepers to the financial system. Failure to perform adequate KYC transfers legal, financial, and reputational risk directly onto the institution.
Over time, KYC evolved from a static compliance checklist into a risk-based control mechanism. Institutions are expected not merely to identify customers, but to understand them proportionately to the risk they present, adjusting scrutiny, monitoring, and controls accordingly.
Related Announcements:
TruTrade Publishes Market Commentary to Explain Why Capital Access Matters More Than Trading Strateg…
What Is Anti-Money Laundering (AML)? Definition, Process, Laws & Examples
What Is UBO Verification? What It Is, Process & Best Practices
Tokenization in Finance: Meaning, How It Works, Benefits, Risks and Regulation
Movitz and Kinexys by J.P. Morgan Launch Global Payee Verification to Prevent Fraud and Misdirected …
GETCHOICE! Surpasses $5 Billion in Annual Utility Spend to Centralize Enterprise Utility Bill Pay an…
Core Components of KYC
KYC is composed of interdependent components that must function together. Weakness in any component compromises the entire framework.
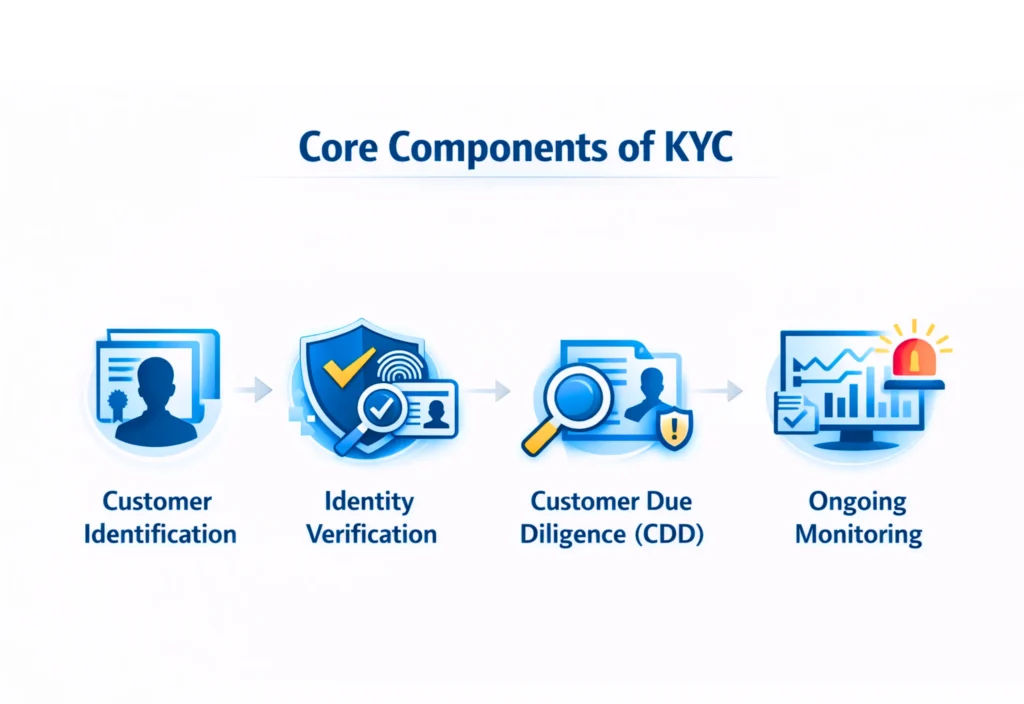
Customer Identification
This component establishes the claimed identity of the customer using reliable, independent source data. For individuals, this typically includes legal name, date of birth, and government-issued identifiers. For entities, it includes legal existence, registration details, and ownership structure.
Identification answers the question of who the customer claims to be, not whether that claim is true.
Identity Verification
Verification tests the authenticity of the claimed identity. This may involve document validation, biometric matching, database checks, or trusted third-party attestations.
Verification answers whether the identity can be proven to exist and belong to the person presenting it.
Customer Due Diligence (CDD)
CDD evaluates the customer’s expected behavior and inherent risk. This includes understanding the nature and purpose of the relationship, expected transaction patterns, geographic exposure, and customer type.
CDD produces a risk rating that determines the intensity of controls applied.
Enhanced Due Diligence (EDD)
EDD applies when customers present higher risk, such as politically exposed persons, complex corporate structures, or high-risk jurisdictions. It requires deeper investigation, additional documentation, and senior approval.
EDD is not discretionary; it is triggered by defined risk thresholds.
Ongoing Monitoring
KYC does not end at onboarding. Ongoing monitoring ensures customer behavior remains consistent with the original risk assessment. Material deviations require review, escalation, or re-verification.
Monitoring closes the loop between identity, behavior, and risk over time.
Who Should Care About KYC
KYC concerns far more than compliance teams. Its impact spans operational, strategic, and product decisions.
Financial institutions must care because KYC failures result in fines, license restrictions, and enforcement actions that can threaten viability.
Fintech companies must care because KYC determines onboarding friction, conversion rates, and geographic expansion feasibility.
Product and engineering teams must care because KYC shapes user flows, data architecture, and vendor dependencies.
Investors must care because weak KYC controls represent hidden regulatory and reputational risk.
Customers indirectly care because KYC affects access to services, onboarding speed, and account continuity.
Institutional Context
Global KYC standards are shaped by bodies such as the Financial Action Task Force, while enforcement and interpretation occur through national regulators including the Financial Crimes Enforcement Network in the United States and equivalent authorities elsewhere. These institutions do not prescribe exact technical implementations, but they set expectations for outcomes, evidence, and accountability.
This institutional design is intentional. KYC must adapt to new technologies, risks, and customer behaviors without constant legislative rewrites.
Related Announcements:
What Is Anti-Money Laundering (AML)? Definition, Process, Laws & Examples
ISX Financial EU PLC Appoints Andreas Artemiou as Chief Risk Officer to Strengthen Risk Governance
Sunflower Bank Launches Sunflower Insurance Solutions to Expand Wealth and Risk Management Services
BX Partners Launches 12 Open-Architecture Portfolio Models on Nitrogen Partner Store to Deliver Risk…
Tokenization vs Hashing Explained: Differences, Use Cases, Security and Compliance
Alkymi Launches Alkymi Private Credit to Automate Complex Loan Data Workflows Across Private Credit
How KYC Works (Step by Step)
KYC operates as a controlled sequence of decisions rather than a single verification action. Each step narrows uncertainty and determines whether the institution can proceed, must apply additional controls, or must refuse the relationship.
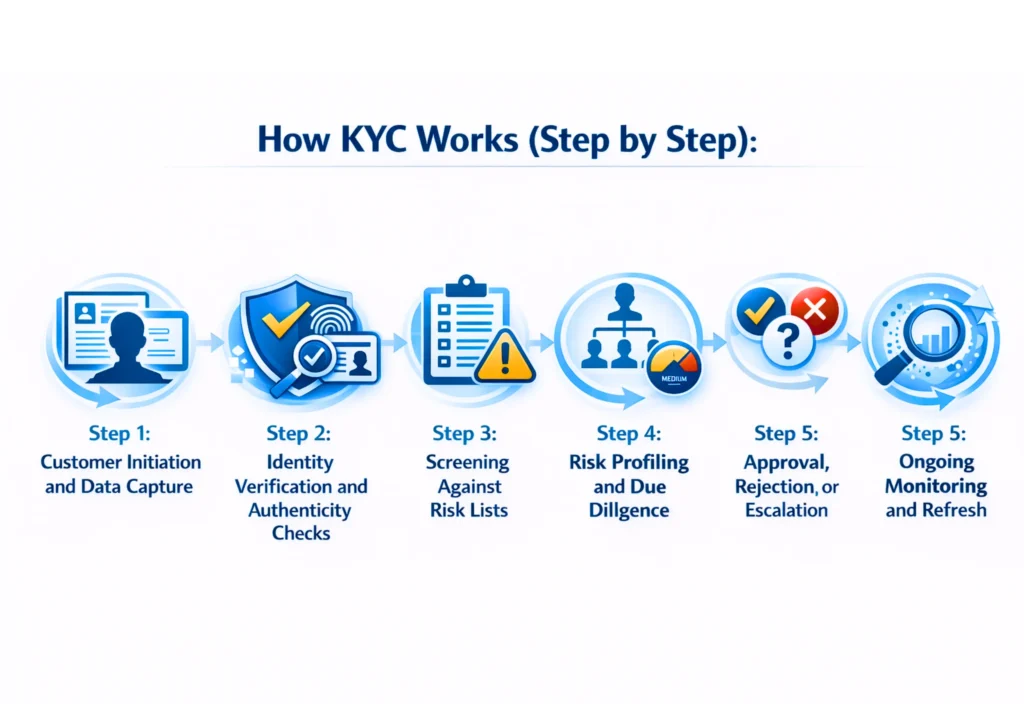
Step 1: Customer Initiation and Data Capture
The process begins when a prospective customer requests access to a regulated financial product. At this point, the institution collects minimum identifying information required by law and internal policy.
For individuals, this typically includes legal name, date of birth, residential address, nationality, and government-issued identification details. For legal entities, it includes registered name, incorporation details, business address, and ownership information.
This step is intentionally inclusive. Institutions collect more data than they immediately validate because later stages determine which elements are material based on risk.
Step 2: Identity Verification and Authenticity Checks
Once data is captured, verification systems test whether the claimed identity corresponds to a real, unique, and valid person or entity.
Verification may include document authenticity checks, database cross-referencing, biometric matching, and device or network consistency analysis. The objective is not convenience but evidentiary reliability. A document that cannot be independently validated has no regulatory value.
At this stage, the institution determines whether the identity exists and whether it plausibly belongs to the applicant.
Step 3: Screening Against Risk Lists
Verified identities are screened against sanctions lists, watchlists, adverse media datasets, and politically exposed person databases. Screening is deterministic rather than probabilistic. A confirmed match triggers mandatory actions defined by regulation and internal policy.
This step establishes whether the institution is legally permitted to engage with the customer at all.
Step 4: Risk Profiling and Due Diligence
If the customer is eligible, the institution assesses inherent risk. Risk factors typically include customer type, geography, expected transaction behavior, product exposure, and ownership complexity.
The outcome is a risk classification that governs control intensity. Low-risk customers may proceed with simplified measures, while higher-risk customers trigger enhanced due diligence requirements.
Risk profiling is where KYC shifts from identity verification to behavioral expectation setting.
Step 5: Approval, Rejection, or Escalation
Based on verification and risk results, the institution makes one of three decisions.
Approval allows the relationship to begin under defined monitoring conditions. Rejection terminates the process and requires retention of evidence. Escalation routes the case to compliance or senior management for review.
This decision point creates a formal audit record that regulators can later examine.
Step 6: Ongoing Monitoring and Refresh
After onboarding, KYC continues through transaction monitoring, periodic reviews, and event-driven reassessments. Changes in behavior, ownership, or external risk indicators can trigger re-verification or reclassification.
This step ensures KYC remains current rather than fossilized at onboarding.
Key Components in Operational KYC Systems
While KYC is governed by regulation, it is executed through systems. Effective implementation requires coordination across several functional components.
Data Collection and Orchestration
These systems manage customer inputs, document uploads, and consent flows while enforcing completeness and consistency rules.
Verification Engines
Verification engines validate documents, biometrics, and identity attributes using internal rules and external data sources.
Screening and Risk Engines
These components perform sanctions checks, adverse media screening, and risk scoring based on configurable policies.
Case Management and Audit Trails
Every KYC decision generates records. Case management systems document escalations, reviewer actions, and approvals, forming the evidentiary backbone of compliance.
Monitoring and Refresh Controls
Ongoing monitoring tools detect deviations from expected behavior and trigger KYC refresh cycles.
KYC fails when these components operate in isolation rather than as a coordinated control system.
Real-World Examples of KYC in Practice
Retail banks use KYC to verify identity at account opening, assign risk tiers, and monitor transaction behavior over time. Changes in income patterns or geographic activity can trigger reviews.
Payment service providers apply KYC to balance fast onboarding with regulatory exposure, often using tiered access where functionality expands as verification depth increases.
Cryptocurrency exchanges use KYC to control access to trading, custody, and fiat on-ramps, with enhanced scrutiny for higher transaction volumes or withdrawals.
Corporate banks apply KYC at the entity level, including beneficial ownership analysis, source-of-funds validation, and periodic ownership refreshes.
These examples differ operationally but rely on the same underlying control logic.
Related Announcements:
What Is Anti-Money Laundering (AML)? Definition, Process, Laws & Examples
Sunflower Bank Launches Sunflower Insurance Solutions to Expand Wealth and Risk Management Services
GETCHOICE! Surpasses $5 Billion in Annual Utility Spend to Centralize Enterprise Utility Bill Pay an…
What Is ISO 20022? Meaning, How It Works, Benefits & Global Migration Timeline
What are Tokenized Deposits? Meaning, How They Work, Benefits, Risks and Global Adoption
ISX Financial EU PLC Appoints Andreas Artemiou as Chief Risk Officer to Strengthen Risk Governance
Common Use Cases for KYC
KYC is mandatory across a wide range of regulated activities.
Account opening for individuals and businesses
Payment processing and money transmission
Lending and credit issuance
Investment and brokerage services
Digital asset custody and exchange
Cross-border remittances
The specific controls vary by product, but the obligation to identify and understand the customer does not.
Benefits of KYC
KYC provides benefits that extend beyond regulatory compliance when implemented correctly.
It reduces exposure to financial crime by preventing anonymous misuse of services.
It creates defensible audit trails that protect institutions during regulatory examinations.
It enables risk-based allocation of monitoring resources rather than uniform scrutiny.
It improves institutional credibility with regulators, partners, and correspondent banks.
These benefits accrue only when KYC is treated as a system, not a formality.
When KYC Makes Sense and When It Does Not
KYC is essential whenever an institution intermediates value, provides custody, or enables regulated financial activity. In these contexts, identity and accountability are inseparable from service provision.
KYC does not meaningfully apply to unregulated informational services or non-custodial tools where no financial relationship is established. Attempting to impose KYC outside regulated boundaries introduces friction without risk reduction.
Misapplication of KYC is as harmful as under-application, as it increases cost and user abandonment without improving systemic safety.
Cost and Complexity of KYC
KYC imposes both direct and indirect costs.
Direct costs include verification services, screening databases, compliance staff, and system maintenance. These scale with customer volume and risk profile.
Indirect costs include onboarding friction, customer drop-off, delayed revenue realization, and engineering complexity.
Institutions must therefore calibrate KYC depth carefully. Over-engineering increases cost without proportionate risk reduction, while under-engineering creates regulatory exposure.
Effective KYC balances evidentiary sufficiency with operational efficiency, guided by risk rather than uniformity.
(KYC)?
Risks and Limitations of KYC
KYC is a control framework, not a guarantee. Its effectiveness is bounded by data quality, institutional judgment, and the dynamic behavior of customers.
One core limitation is identity authenticity versus intent. KYC can establish who a customer is, but it cannot, on its own, determine how that customer will behave in the future. Legitimate identities can still be used for illicit purposes after onboarding.
Another limitation is data dependency. Verification systems rely on external databases, documents, and records that may be outdated, incomplete, or inconsistent across jurisdictions. Where civil registries are weak or fragmented, KYC accuracy degrades materially.
KYC is also vulnerable to false confidence. Institutions may over-rely on initial verification while underinvesting in ongoing monitoring, creating blind spots as customer risk evolves.
Operationally, KYC introduces friction and exclusion. Strict requirements can disproportionately affect underbanked populations, migrants, and individuals in regions without standardized identity infrastructure.
Finally, KYC scales imperfectly. As customer volumes grow, manual reviews, escalations, and refresh cycles become cost-intensive unless systems are carefully designed around risk prioritization.
Regulatory Perspective on KYC
KYC obligations are not defined by a single global law but by a layered regulatory architecture.
At the global level, standards are shaped by the Financial Action Task Force, which sets expectations for customer due diligence, risk-based approaches, and ongoing monitoring. These standards are intentionally principle-based rather than prescriptive.
At the national level, regulators translate these principles into enforceable rules. In the United States, KYC requirements are embedded within the Bank Secrecy Act framework and enforced by bodies such as the Financial Crimes Enforcement Network. In other jurisdictions, equivalent authorities perform the same role with local variations.
A critical regulatory expectation is evidence. Institutions must not only perform KYC but must be able to demonstrate how and why decisions were made, including risk ratings, escalations, and approvals.
Regulators also emphasize proportionality. Institutions are expected to apply controls commensurate with risk, not uniformly across all customers. Failure to calibrate controls appropriately is a common source of enforcement action.
Related Announcements:
Tokenization in Finance: Meaning, How It Works, Benefits, Risks and Regulation
What Is Anti-Money Laundering (AML)? Definition, Process, Laws & Examples
What are Tokenized Deposits? Meaning, How They Work, Benefits, Risks and Global Adoption
What Is Know Your Business (KYB)? Definition, Process & Compliance
TruTrade Publishes Market Commentary to Explain Why Capital Access Matters More Than Trading Strateg…
GETCHOICE! Surpasses $5 Billion in Annual Utility Spend to Centralize Enterprise Utility Bill Pay an…
KYC vs Related Concepts
KYC vs AML
KYC is a foundational component of AML but does not encompass the entire AML program. KYC establishes identity and baseline risk, while AML extends into transaction monitoring, investigations, reporting, and law enforcement cooperation. Treating KYC as a substitute for AML is a structural compliance error.
KYC vs KYB
KYC focuses on natural persons, while Know Your Business applies to legal entities. KYB introduces additional complexity, including corporate registries, beneficial ownership analysis, and control structures. Both share the same risk-based philosophy but operate on different identity primitives.
KYC vs Identity Verification
Identity verification is a technical activity within KYC. KYC includes verification but extends into risk assessment, monitoring, and governance. Verification without KYC context produces data, not compliance.
When KYC Creates Value and When It Becomes a Burden
KYC creates value when it is tightly aligned with product risk. High-value, high-liability products benefit from deeper identity and due diligence controls because potential harm is significant.
KYC becomes a burden when controls exceed the risk profile of the product or customer. Excessive documentation, repeated checks, or unnecessary refreshes increase abandonment and cost without reducing systemic risk.
Institutions that treat KYC as a static checklist tend to accumulate friction. Institutions that treat it as a dynamic control system adapt more effectively as risk changes.
Adoption Timeline of KYC
KYC adoption has evolved in distinct phases.
In early banking systems, identity verification was manual and localized, relying on in-person relationships and paper records.
As financial systems globalized, KYC became formalized through regulations responding to cross-border crime and terrorism financing.
The rise of digital finance forced KYC into remote, automated workflows, introducing electronic verification, biometrics, and third-party data providers.
Current adoption reflects a hybrid model, combining automation with targeted human review, driven by risk rather than volume.
This evolution continues as customer behavior, technology, and regulatory expectations change.
Future Outlook for KYC
The future of KYC is shaped less by regulation and more by operational pressure.
Institutions are moving toward continuous KYC, where identity and risk are reassessed dynamically rather than at fixed intervals.
Data interoperability and standardized identity frameworks are gaining attention, particularly where regulators seek to reduce duplication without lowering standards.
At the same time, regulators are increasing scrutiny of model risk, data sourcing, and explainability in automated KYC decisions.
The trajectory points toward tighter integration between identity, behavior, and risk, rather than radical deregulation or elimination of KYC.
Key Takeaways
KYC is a continuous control framework, not a one-time onboarding task.
Identity verification alone does not constitute KYC.
Risk-based application is central to regulatory expectations.
Weak KYC creates systemic exposure; excessive KYC creates friction without benefit.
The effectiveness of KYC depends on integration across systems, processes, and governance.
Frequently Asked Questions About KYC
What does KYC mean?
KYC stands for Know Your Customer.
It refers to the legally mandated process by which financial institutions identify, verify, assess, and continuously monitor customers to ensure they are who they claim to be and do not pose unacceptable financial crime risk.
In practice, KYC establishes identity, legitimacy, and risk ownership before and during a financial relationship.
What are the 3 components of KYC?
The three core components of KYC are:
Customer Identification
Collecting basic identity information such as name, date of birth, address, and legal identifiers.
Customer Due Diligence (CDD)
Assessing customer risk based on profile, geography, expected activity, and product usage.
Ongoing Monitoring
Continuously reviewing transactions and behavior to ensure they remain consistent with the assessed risk.
Without all three, KYC is incomplete.
What are the 5 stages of KYC?
The five commonly recognized stages of KYC are:
Customer Identification – collecting identity information
Identity Verification – validating identity using reliable sources
Risk Assessment – classifying the customer’s risk level
Enhanced Due Diligence (if required) – deeper checks for higher-risk customers
Ongoing Monitoring and Review – continuous reassessment over time
These stages operate sequentially but feed into each other throughout the customer lifecycle.
How do you explain KYC in an interview?
A strong interview explanation is:
“KYC is a regulatory framework used by financial institutions to identify customers, verify their identities, assess their risk, and continuously monitor their activities to prevent financial crime and comply with AML laws.”
Interviewers look for clarity, not jargon. Mention identity, risk, and ongoing monitoring explicitly.
What are the 4 keys of KYC?
The four key pillars of KYC are:
Identity – knowing who the customer is
Verification – proving the identity is real and valid
Risk Understanding – knowing how risky the customer is
Monitoring – ensuring behavior stays within expected boundaries
These four keys ensure KYC is both defensible and effective.
What are the 5 main questions asked in a KYC interview?
Interviewers typically test whether you understand KYC by probing:
What is KYC and why is it required?
How does KYC differ from AML?
What documents or data are used for KYC?
What triggers Enhanced Due Diligence?
Why is ongoing monitoring necessary after onboarding?
These questions assess conceptual clarity, not memorization.
How many types are in KYC?
There are three primary types of KYC:
Simplified Due Diligence (SDD) – for low-risk customers
Customer Due Diligence (CDD) – standard KYC for most customers
Enhanced Due Diligence (EDD) – for high-risk customers
The type applied depends on the customer’s risk profile, not convenience.
What is 6-point KYC?
6-point KYC is a method used in some jurisdictions to verify identity by assigning weighted points to identity documents.
For example:
Passport: higher points
Utility bill or ID card: lower points
A customer must accumulate six or more points using approved documents to meet identity verification requirements.
It is a verification mechanism, not a full KYC program.
What are the 4 primary objectives of KYC?
The four primary objectives of KYC are:
Prevent financial crime such as money laundering and fraud
Comply with regulatory requirements
Understand customer risk before and during relationships
Protect the integrity of the financial system
All KYC controls ultimately serve these objectives.
Sources:
Financial Action Task Force (FATF) — Guidance on customer due diligence and risk-based approach
https://www.fatf-gafi.org
U.S. Financial Crimes Enforcement Network (FinCEN) — Customer Due Diligence Rule and KYC obligations
https://www.fincen.gov
European Banking Authority (EBA) — Guidelines on customer due diligence and AML/CFT
https://www.eba.europa.eu
Bank for International Settlements (BIS) — Sound practices on AML/CFT and customer identification
https://www.bis.org
UK Financial Conduct Authority (FCA) — KYC and AML supervision framework
https://www.fca.org.uk
Last Updated
December 20, 2025
Readers can explore more Fintech Explainers HERE.
Click HERE to explore more.
