Know Your Business (KYB) is a regulatory and risk-management process through which financial institutions verify, understand, and continuously monitor business customers by validating legal existence, ownership, control, operational legitimacy, and risk exposure to prevent fraud, money laundering, terrorism financing, and regulatory breaches.

One-Sentence Definition of Know Your Business (KYB)
Know Your Business (KYB) is the institutional discipline of identifying, verifying, and monitoring commercial entities across their lifecycle by mapping corporate structure, beneficial owners, authorized signatories, jurisdictions, and transactional behavior to ensure compliance, transparency, and defensible risk decisions in regulated financial ecosystems.
What Is Know Your Business (KYB)
Know Your Business (KYB) is the formal, regulator-mandated process through which financial institutions, fintech platforms, payment service providers, crypto exchanges, banks, lenders, and regulated intermediaries identify, verify, understand, and continuously monitor business customers to prevent financial crime, regulatory breaches, and systemic risk. KYB extends the principles of Know Your Customer (KYC) from individuals to legal entities, recognizing that companies, partnerships, trusts, foundations, and other organizational structures can be misused as vehicles for money laundering, fraud, terrorist financing, sanctions evasion, and tax crimes.
At its core, KYB answers three non-negotiable questions about any business relationship:
- Who is the business in legal reality, not just by name but by registration, ownership, control, and governance
- Who ultimately owns and controls the business, including beneficial owners, directors, and authorized signatories
- Whether the business operates lawfully and transparently over time, across jurisdictions, transactions, and counterparties
KYB is not a single check, document request, or onboarding form. It is a structured compliance framework that combines legal verification, risk assessment, ownership transparency, sanctions screening, and ongoing monitoring throughout the lifecycle of a business relationship. Regulators treat KYB as essential because corporate entities can obscure identity, layer ownership, and move capital at scale, making them higher-impact risk vectors than individuals.
A complete KYB framework typically covers:
- Business identity verification (legal name, registration number, incorporation details)
- Corporate structure analysis (subsidiaries, parents, holding entities)
- Ultimate Beneficial Owner (UBO) identification and verification
- Director, officer, and signatory screening
- Business activity validation and industry risk classification
- Geographic exposure and jurisdictional risk assessment
- Continuous monitoring for changes, anomalies, and red flags
KYB exists to collapse institutional uncertainty around business customers. Any definition that frames KYB as “company document collection” or “corporate KYC” is incomplete. KYB is the compliance infrastructure that allows institutions to onboard, serve, and transact with businesses without enabling hidden financial crime.
KYB as a regulatory obligation
From a regulatory perspective, KYB is a mandatory legal duty, not a best practice or optional safeguard. Financial regulators worldwide require institutions to perform KYB to comply with anti-money laundering (AML), counter-terrorist financing (CTF), sanctions, and financial integrity laws. Failure to implement adequate KYB controls exposes institutions to fines, license restrictions, enforcement actions, and reputational damage.
Regulatory KYB obligations typically require institutions to:
- Identify and verify the legal existence of the business customer
- Establish and verify beneficial ownership above defined thresholds
- Understand the nature and purpose of the business relationship
- Assess inherent and residual business risk before onboarding
- Apply enhanced due diligence to high-risk entities and sectors
KYB is enforced because businesses can:
- Act as shells to disguise true ownership
- Facilitate large-value, cross-border financial flows
- Obscure proceeds of crime through complex structures
Regulators therefore view KYB as a first-line defense against systemic financial abuse, making it a foundational compliance requirement rather than a procedural formality.
KYB as an operational compliance system
Operationally, KYB functions as a living compliance system embedded into onboarding, transaction processing, account management, and risk governance workflows. It is not confined to compliance teams alone; it intersects with product design, payments operations, credit underwriting, treasury, and customer support.
An operational KYB system typically includes:
- Automated business verification and registry data ingestion
- Ownership and control mapping across multi-layer entities
- Sanctions, PEP, and adverse-media screening at entity and individual levels
- Risk scoring models tailored to business type, size, and geography
- Internal escalation, review, and approval workflows
In practice, KYB enables institutions to:
- Decide whether to onboard or reject a business
- Set transaction limits and controls aligned to risk
- Trigger enhanced monitoring for sensitive activities
- Maintain auditable compliance records for regulators
Without operational KYB, compliance becomes fragmented, manual, and reactive. With it, institutions achieve scalable, defensible compliance that supports growth without sacrificing regulatory control.
KYB as a continuous business-risk control
Critically, KYB is not static. Businesses evolve, ownership changes, activities expand, and risk profiles shift over time. KYB therefore operates as a continuous business-risk control, not a one-time onboarding exercise.
Ongoing KYB monitoring focuses on:
- Changes in ownership, directors, or control rights
- Sudden shifts in transaction behavior or volumes
- Expansion into new geographies or industries
- Emerging sanctions, enforcement actions, or negative news
- Mismatches between stated business purpose and actual activity
This continuous approach allows institutions to:
- Detect risk escalation early
- Re-classify customers dynamically
- Apply enhanced due diligence when needed
- Exit relationships that become non-compliant
In this sense, KYB acts as an early-warning system for institutional exposure. It protects not only regulatory standing, but also financial stability, platform integrity, and long-term trust in the financial ecosystem.
What Know Your Business (KYB) Is NOT
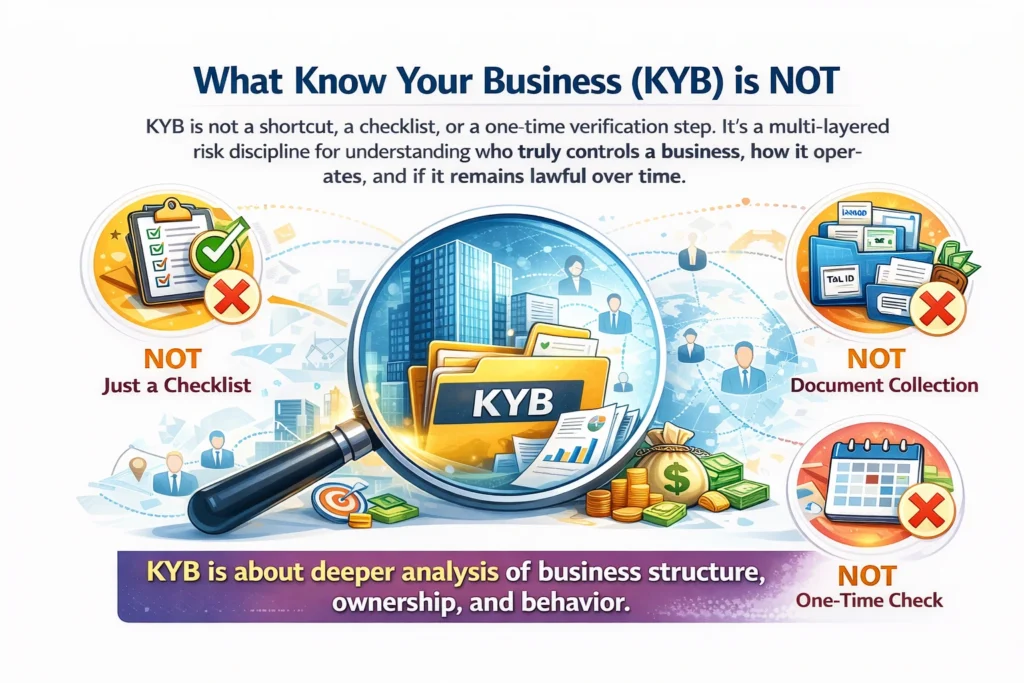
Know Your Business (KYB) is frequently misunderstood, oversimplified, or incorrectly framed in both regulatory discussions and product marketing. To build a correct mental model, it is as important to define what KYB is not as it is to explain what it is. KYB is not a shortcut, a checklist, or a lightly modified version of existing compliance frameworks. It is a distinct, multi-layered risk discipline designed to address the structural opacity, ownership complexity, and behavioral risk of legal entities operating within the financial system.
KYB is not a cosmetic compliance exercise meant to satisfy auditors or regulators at the lowest possible cost. It does not exist to collect documents for storage, nor to generate a static “verified” badge for a business account. Treating KYB in this manner leads to systemic blind spots, regulatory exposure, and downstream financial crime risk.
At its core, KYB is about answering hard, persistent questions about a business entity over time:
- Who truly owns and controls the business, not just on paper but in practice
- How the business generates value and moves money, across products, geographies, and counterparties
- Whether the business’s behavior remains lawful, explainable, and consistent as it scales, pivots, or restructures
Mischaracterizing KYB creates dangerous assumptions, such as believing that a single verification step is sufficient, or that business risk can be reduced to registry data alone. These assumptions fail in the real world, where shell companies, nominee directors, layered ownership structures, and rapid operational changes are common.
Understanding what KYB is not helps prevent three critical failures:
- Underestimating business-level financial crime risk
- Over-relying on static or point-in-time checks
- Confusing identity validation with risk intelligence
The sections below address the three most common and costly misconceptions about KYB, each of which undermines effective compliance when left uncorrected.
KYB is not KYC applied to businesses
KYB is not a simple extension of Know Your Customer (KYC) workflows to legal entities. While KYC focuses on identifying a natural person, KYB must assess organizational reality, not individual identity alone. Businesses are dynamic systems, not static subjects.
Key differences often overlooked include:
- Businesses have multiple controlling parties, not a single identity
- Ownership can be indirect, layered, or jurisdictionally fragmented
- Risk emerges from operations and transactions, not just identity data
Applying consumer-style KYC logic to businesses ignores corporate governance, control mechanisms, and economic behavior. KYB requires entity-level reasoning, not person-level substitution.
KYB is not document or registry verification
KYB is not limited to collecting incorporation certificates, tax IDs, or registry extracts. Documents describe what a business claims to be, not how it actually operates. Registries are often outdated, incomplete, or structurally incapable of revealing true control.
Relying solely on documents fails because:
- Nominee directors can mask real decision-makers
- Beneficial ownership data may be stale or inaccurate
- Documents do not explain transaction patterns or revenue logic
KYB goes beyond documentation to validate substance over form, combining records with behavioral and contextual analysis.
KYB is not a one-time onboarding requirement
KYB is not a one-off task completed at onboarding and forgotten thereafter. Businesses evolve continuously, and risk evolves with them. Ownership changes, new products launch, geographies expand, and transaction behavior shifts—often rapidly.
Treating KYB as a single checkpoint ignores:
- Post-onboarding ownership or control changes
- Business model drift into higher-risk activities
- Emerging regulatory or sanctions exposure
Effective KYB is a continuous lifecycle process, requiring ongoing monitoring, reassessment, and contextual updates to ensure that a business remains legitimate, compliant, and explainable over time.
Why Know Your Business (KYB) Exists
Know Your Business (KYB) exists because modern financial systems are built on legal entities, not people, and legal entities introduce layers of opacity, leverage, delegation, and jurisdictional complexity that individual identity controls cannot capture. Unlike retail customers, businesses operate as structured abstractions—they can own assets, open multiple accounts, enter contracts, move capital across borders, delegate authority, and persist indefinitely regardless of changes in ownership or management. This structural reality creates a systemic risk gap that KYC alone cannot close.
At its core, KYB exists to resolve institutional uncertainty. When a bank, payment processor, fintech platform, or regulated intermediary onboards a company, the true counterparty risk is not the signatory on the account but the entity itself: its legal formation, control structure, economic beneficiaries, operational behavior, and regulatory posture. KYB formalizes the process of identifying, validating, and continuously understanding that entity in legally enforceable terms.
KYB also exists because businesses are the primary vehicles of financial crime at scale. Large-value money laundering, sanctions evasion, trade-based fraud, tax evasion, terrorist financing, and regulatory arbitrage overwhelmingly occur through corporate shells, partnerships, trusts, and complex ownership chains—not through single individuals acting alone. Without KYB, institutions are blind to how capital actually flows through the economy.
From a regulatory perspective, KYB exists to enforce accountability alignment. Regulators require institutions to demonstrate that they know:
- Who legally owns and controls an entity
- Who ultimately benefits economically
- Who has authority to act on behalf of the business
- Whether the business activity is lawful, consistent, and explainable
KYB therefore functions as a risk normalization layer. It converts an abstract legal construct into a verified, monitorable, and auditable risk profile that can be assessed, priced, restricted, or exited over time. Without KYB, institutions cannot defend themselves against enforcement actions, reputational damage, or systemic exposure arising from opaque corporate behavior.
In short, KYB exists because business risk is not human risk. It is structural, scalable, and persistent—and it requires a dedicated control framework designed specifically for legal entities.
Structural risk asymmetry of legal entities
Legal entities introduce a structural risk asymmetry because they separate control, ownership, benefit, and liability across multiple layers. Unlike individuals, a business can be owned by one party, controlled by another, managed by a third, and economically benefited by yet another—often across jurisdictions. This fragmentation creates blind spots that criminals and bad actors exploit.
Key sources of asymmetry include:
- Multi-tier ownership chains spanning subsidiaries and holding companies
- Nominee directors and shareholders obscuring true control
- Cross-border incorporation arbitrage
- Perpetual existence independent of natural persons
- Limited liability shielding individuals from direct accountability
KYB exists to collapse this asymmetry by reconstructing the entity into a single, intelligible risk object. Without entity-level verification, institutions face an uneven risk surface where exposure grows while visibility declines.
Why individuals cannot represent business risk
Individuals cannot represent business risk because authority is not equivalent to ownership or benefit. The person opening an account or signing documents may have operational authority but no economic stake, no long-term control, and no exposure to downstream consequences. Treating that individual as the risk proxy produces false confidence.
Critical mismatches include:
- Authorized signatories who are employees, not owners
- Directors acting under board mandates
- Agents acting on power of attorney
- Founders diluted by later investment rounds
Business risk resides in the entity’s structure and activity, not in the identity of a single human actor. KYB corrects this error by shifting risk assessment from “who is acting” to “what system they are acting within.”
Financial crime vectors unique to businesses
Businesses enable financial crime vectors that are structurally impossible for individuals. Scale, repetition, contractual legitimacy, and operational complexity allow illicit activity to blend into normal commerce. KYB exists to detect and disrupt these entity-specific pathways.
Common business-only crime vectors include:
- Shell companies used for layering and integration
- Trade-based money laundering via false invoicing
- Complex ownership webs for sanctions evasion
- Abuse of correspondent banking relationships
- Tax evasion through profit shifting and transfer pricing
These risks are embedded in how businesses operate, not merely in who operates them. KYB provides the analytical framework to evaluate whether a company’s legal form, ownership logic, and transactional behavior align with lawful economic purpose—or signal concealed criminal intent.
How Know Your Business (KYB) Works (End-to-End)
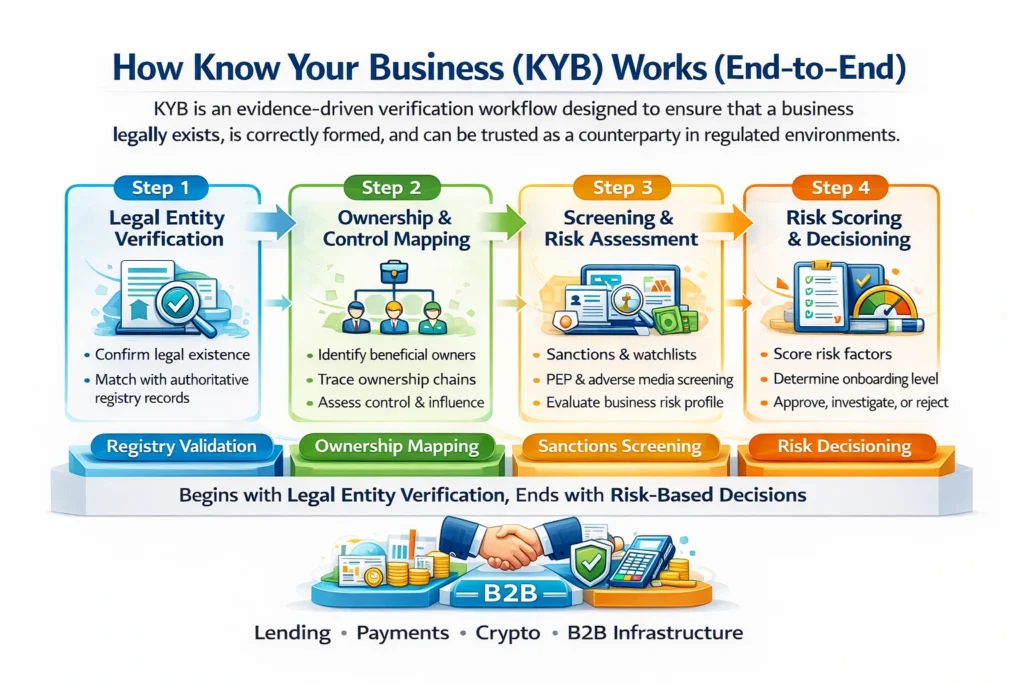
Know Your Business (KYB) operates as a deterministic, evidence-driven verification workflow designed to establish whether a business legally exists, is correctly formed, and can be trusted as a counterparty in regulated financial, payments, lending, crypto, and B2B infrastructure environments. End-to-end KYB is not a single check or document request; it is a layered validation system that starts with legal existence and progressively reduces uncertainty across ownership, control, risk exposure, and ongoing behavior.
At the core of KYB is one foundational truth: if legal existence is not conclusively proven, every downstream control fails. Beneficial ownership, sanctions screening, transaction monitoring, tax reporting, and risk scoring all presuppose that the entity itself is real, correctly incorporated, and recognized by an authoritative registry. This is why every KYB program—regardless of jurisdiction, industry, or institution size—begins with legal entity existence and registry validation.
End-to-end KYB therefore follows a strict logical order:
- Establish that the entity exists in law
- Confirm that its formation details align with registry records
- Validate jurisdictional legitimacy and entity type
- Assess the reliability of the source data itself
- Only then proceed to ownership, control, and risk layers
Step 1: Legal entity existence and registry validation
Legal entity existence and registry validation is the point of entry into KYB. Its objective is not to assess risk, intent, or behavior, but to answer a far more basic and non-negotiable question: Does this business legally exist in the real world, in the jurisdiction it claims, in the form it claims?
This step involves verifying the entity against an authoritative government or quasi-government registry and confirming that the submitted business identity matches official records without material discrepancies. The output of this step is binary in nature—either the entity exists as claimed, or it does not—but the process itself requires careful interpretation and structured cross-checks.
Key validation dimensions at this stage include:
- Exact legal name and registered name equivalence
- Registration or incorporation number validity
- Jurisdiction of formation and governing authority
- Legal entity type and formation logic
- Entity status (active, dissolved, struck off, dormant)
Critically, this step does not rely on self-attested documents alone. Certificates of incorporation, business licenses, or tax IDs are treated as supporting artifacts, not primary truth sources. The registry record is the source of truth, and every KYB control downstream assumes its correctness.
Jurisdiction, incorporation logic, entity types
Jurisdiction and entity type validation ensures that the business is legally capable of existing and operating in the form it claims under the laws of its incorporation. Different jurisdictions permit different entity structures, naming conventions, and operational scopes, and KYB must evaluate the entity within that legal context.
Key jurisdictional and formation checks include:
- Country or state of incorporation consistency with registry authority
- Permissible entity types within that jurisdiction (e.g., LLC, LLP, PLC, GmbH)
- Alignment between declared business structure and registry-recognized form
- Legal naming rules, suffixes, and abbreviations compliance
- Recognition of foreign entities, branches, or subsidiaries
Entity type validation is essential because rights, obligations, and ownership rules vary materially by structure. A sole proprietorship, private limited company, and partnership each carry different disclosure, liability, and control implications, all of which directly affect subsequent KYB steps.
Registry reliability and data limitations
Registry validation is only as strong as the reliability, freshness, and completeness of the underlying registry data. Not all registries are equal, and KYB systems must explicitly account for structural limitations in public data sources.
Common registry reliability considerations include:
- Update frequency delays between filing and public visibility
- Limited disclosure of shareholders or directors
- Manual or paper-based registry systems
- Language, transliteration, and formatting inconsistencies
- Historical data gaps for older entities
Effective KYB frameworks do not assume registry infallibility. Instead, they apply confidence weighting to registry outputs and flag jurisdictions where supplemental verification or enhanced due diligence may be required. Recognizing registry limitations is a core professional competency in KYB, not a secondary concern.
Deep operational mechanics of entity existence validation
Beyond surface-level confirmation, professional KYB programs perform structured reconciliation between registry data and submitted business information to detect inconsistencies that may signal error, misrepresentation, or fraud. This reconciliation is deterministic, rule-based, and auditable.
Operational reconciliation typically evaluates:
- Exact string matching vs acceptable legal name variations
- Registration number format and checksum logic
- Address normalization across registry and customer input
- Date coherence between incorporation date and business history claims
- Entity status transitions (active → dissolved → reactivated)
This step also establishes the entity identity anchor used across all KYB subsystems. The registry identifier becomes the primary key that links:
- Beneficial ownership graphs
- Sanctions and watchlist screening
- Adverse media monitoring
- Transaction monitoring attribution
- Regulatory reporting and audit trails
Failure at this stage results in hard stops, not soft warnings. An entity that cannot be conclusively validated at the registry level cannot progress through KYB, regardless of commercial pressure or customer value.
From a regulatory and risk standpoint, this rigor exists because non-existent or improperly formed entities are the highest-risk counterparties by definition. Shell entities, dissolved companies, impersonated firms, and fabricated registrations all exploit weak entry controls. Step 1 is specifically designed to collapse that attack surface before any financial exposure occurs.
In mature KYB systems, legal entity existence validation is therefore:
- Mandatory
- Non-delegable
- Fully documented
- Independently reproducible
- Continuously re-verifiable
Without this foundation, KYB ceases to be a control system and becomes a paperwork exercise.
Step 2: Beneficial ownership and control mapping
Beneficial ownership and control mapping is the operational core of KYB, where an institution moves beyond surface-level registration data to identify the real human beings who ultimately own, control, or materially influence a business. This step establishes who stands behind the legal entity and whether those individuals present financial crime, sanctions, reputational, or regulatory risk. The objective is not merely to list shareholders, but to create a complete, explainable ownership and control graph that regulators can audit.
In practice, this step requires institutions to:
- Identify all natural persons meeting beneficial ownership thresholds under applicable regulations
- Map direct and indirect equity ownership across all intermediate entities
- Identify control rights independent of ownership percentages
- Assess influence exercised through voting agreements, veto rights, or management authority
Key activities typically include:
- Collecting ownership declarations and corporate documents
- Tracing shareholding chains across jurisdictions
- Validating ownership percentages and control mechanisms
- Reconciling inconsistencies between disclosed and observed control
This step is critical because financial crime risk concentrates at the beneficial owner level, not the entity shell. Accurate ownership and control mapping enables effective AML risk scoring, sanctions screening, PEP identification, and ongoing monitoring. Without this step, KYB collapses into a formality rather than a risk control function.
Ownership vs control vs influence
Ownership, control, and influence are distinct concepts that must be assessed separately during KYB, even though they often overlap. Ownership refers to economic interest, typically measured by shareholding or equity percentage. Control refers to the legal or contractual power to direct business decisions. Influence captures informal or indirect power that may not appear in corporate filings.
In KYB assessments, institutions evaluate:
- Ownership: equity stakes, profit rights, and capital exposure
- Control: board appointments, voting rights, veto powers, signatory authority
- Influence: founder dominance, familial relationships, nominee arrangements
A person may control a company without owning it, or influence it without formal authority. Regulators expect firms to identify all three dimensions because financial crime actors frequently exploit gaps between ownership and control to obscure accountability and evade detection.
Layered and obscured ownership structures
Layered and obscured ownership structures are a primary KYB risk indicator and a common tactic used to conceal beneficial owners. These structures involve multiple legal entities stacked across jurisdictions, often mixing operating companies, holding companies, trusts, foundations, and special purpose vehicles. Each additional layer increases opacity and investigative complexity.
Common characteristics include:
- Multi-jurisdiction ownership chains
- Use of nominee shareholders or directors
- Interposition of trusts or private foundations
- Circular or cross-shareholding arrangements
Effective KYB requires institutions to unwind every layer until natural persons are identified, regardless of complexity. This includes validating source documents, applying ownership thresholds cumulatively, and assessing whether complexity itself indicates elevated risk. Regulators view unexplained complexity as a red flag, making thorough ownership de-layering a non-negotiable KYB obligation.
Step 3: Directors, officers, and controlling persons
This step focuses on identifying, validating, and risk-assessing the individuals who exercise authority, control, or significant influence over a business entity. KYB does not stop at entity registration; it must extend to natural persons who can direct financial activity, approve transactions, or materially influence operations. This includes directors, executive officers, senior management, authorized signatories, and any individual meeting ownership or control thresholds. Institutions must map formal governance roles against actual decision-making power to avoid nominal compliance.
Key objectives of this step include:
- Identifying all directors, officers, and controlling persons per jurisdictional thresholds
- Verifying identity, role legitimacy, and appointment authority
- Assessing whether control is direct, indirect, or exercised through proxies
- Aligning governance records with ownership and operational reality
- Detecting concealed influence, shadow directors, or nominee arrangements
Failure at this stage creates structural blind spots that enable fraud, regulatory evasion, and accountability dilution.
Role-based authority risk
Role-based authority risk arises when individuals possess transaction or governance power disproportionate to their disclosed role. Senior officers, authorized signatories, or delegated controllers may execute high-risk actions without sufficient scrutiny. KYB must evaluate:
- Scope of decision-making authority
- Financial and operational access rights
- Ability to override controls or approvals
Unchecked authority concentration materially increases exposure to fraud, misuse, and regulatory breaches.
Cross-border visibility gaps
Cross-border visibility gaps occur when directors or controlling persons operate across jurisdictions with inconsistent disclosure, registry quality, or enforcement standards. These gaps obscure true control and accountability. Common risk drivers include:
- Foreign-based directors in low-transparency jurisdictions
- Fragmented corporate filings across countries
- Limited access to beneficial ownership registries
Effective KYB must reconcile multi-jurisdictional records to prevent regulatory arbitrage and hidden control structures.
Step 4: Sanctions, PEP, and adverse media screening
Sanctions, PEP, and adverse media screening is the control layer that determines whether an identified party is legally, politically, or reputationally restricted from engagement. Once identity verification establishes who the customer is, this step evaluates whether the relationship is permissible, conditionally acceptable, or explicitly prohibited. Screening is conducted against global sanctions lists, politically exposed person databases, and continuously refreshed adverse media sources covering enforcement actions, corruption, fraud, terrorism, and broader financial crime exposure.
This step serves three core purposes:
- preventing interactions with sanctioned individuals, entities, or jurisdictions
- identifying elevated risk arising from political power, influence, or public office
- surfacing negative media that signals misconduct, litigation, or regulatory scrutiny
Operationally, screening is not a single checkpoint. It occurs at onboarding, during periodic reviews, and on an ongoing basis as sanctions lists and media datasets evolve. Matches are risk-scored, contextualized, and escalated using factors such as jurisdiction, ownership links, exposure severity, and intended activity. The outcome informs approval decisions, enhanced due diligence requirements, monitoring intensity, or mandatory rejection, anchoring both regulatory compliance and reputational protection.
Entity vs individual screening logic
Screening logic differs fundamentally between natural persons and legal entities. Individuals are evaluated directly using name-based sanctions data, PEP status, aliases, nationality, and date-of-birth attributes. Entities require a layered approach that extends beyond the registered name to beneficial owners, directors, controlling persons, subsidiaries, and parent organizations.
Effective entity screening therefore:
- resolves ownership and control hierarchies
- screens all materially connected individuals
- assesses jurisdictional and sector exposure
This structure-based analysis captures indirect sanctions risk that simple name matching cannot detect.
False positives and ambiguity handling
False positives arise from common names, transliteration variance, incomplete identifiers, and fuzzy matching thresholds. Mature compliance programs treat ambiguity as an operational challenge rather than a regulatory weakness. Potential matches are contextualized using geography, age, role, ownership percentage, and corroborating identifiers.
Effective handling relies on:
- confidence scoring with documented rationale
- trained analyst review and consistent resolution standards
- audit-ready decision trails
Clear disposition frameworks reduce alert fatigue while preserving defensibility, ensuring genuine risk is escalated and benign matches are systematically cleared.
Step 5: Risk scoring and decisioning
Risk scoring and decisioning convert all prior KYB, KYC, and AML signals into an enforceable compliance outcome. At this stage, institutions aggregate identity verification results, ownership clarity, sanctions screening, adverse media, transaction intent, geography, industry risk, and behavioral indicators into a unified risk profile. Scores are calculated using weighted factors aligned to regulatory expectations and internal risk appetite. Decisioning then applies policy logic to determine onboarding approval, conditional approval, enhanced due diligence, or rejection. Effective implementations emphasize explainability, auditability, and consistency across channels and jurisdictions. Outputs must be defensible to regulators and actionable for operations teams. A mature framework typically includes:
- normalized risk attributes with documented weightings
- score bands mapped to clear actions
- automated approvals for low risk
- mandatory EDD triggers for elevated risk
- manual review workflows for edge cases
- full decision logs for audits and model governance
Deterministic vs probabilistic models
Deterministic models rely on fixed rules, thresholds, and boolean logic to assign risk outcomes, producing consistent and easily explainable decisions. Probabilistic models use statistical methods and machine learning to estimate likelihood of risk based on patterns and correlations. While deterministic approaches favor regulatory transparency and predictability, probabilistic models improve sensitivity, adaptiveness, and detection of complex risk signals when governed properly under strong compliance oversight.
EDD escalation thresholds
EDD escalation thresholds define when standard due diligence becomes insufficient and deeper investigation is mandatory. Thresholds are commonly triggered by high composite risk scores, opaque ownership, high-risk jurisdictions, regulated industries, sanctions proximity, or adverse media severity. Clear thresholds ensure consistency, prevent analyst discretion drift, and demonstrate proportional risk treatment to regulators during examinations. They also support defensible audit trails and timely, compliant escalation decisions.
Step 6: Ongoing monitoring and KYB refresh
Ongoing monitoring and KYB refresh ensure that a previously verified business remains legitimate, explainable, and compliant as its risk profile evolves. This step moves KYB from a one-time onboarding exercise into a continuous risk management discipline embedded across the entire customer lifecycle. It focuses on detecting changes that materially alter ownership, control, geography, operational behavior, or exposure to financial crime risk. Effective ongoing KYB combines automated surveillance, structured data refreshes, and human review to prevent stale assumptions and hidden compliance gaps.
Core activities include:
- Continuous screening against sanctions lists, PEP databases, adverse media, and regulatory watchlists
- Monitoring transactional behavior against expected business models and declared activity
- Detecting ownership, UBO, or management changes through corporate registry updates
- Re-scoring risk levels and dynamically adjusting controls, limits, and due-diligence depth
Without this step, institutions accumulate invisible risk that often surfaces only during audits, investigations, or enforcement actions, leading to regulatory penalties, financial losses, and long-term reputational damage.
Trigger-based vs periodic reviews
Trigger-based and periodic KYB reviews define when a business must be reassessed. Trigger-based reviews are event-driven and activate when specific risk signals occur. These include ownership or UBO changes, jurisdictional shifts, abnormal transaction patterns, negative media exposure, or regulatory alerts. Periodic reviews, by contrast, occur on fixed review cycles determined by the customer’s assigned risk tier. High-risk entities require frequent refreshes and deeper reassessment, while low-risk businesses follow longer, less intensive review intervals aligned with regulatory expectations.
Why static KYB fails over time
Static KYB fails because businesses are not static entities. Ownership structures evolve, directors change, revenue models pivot, and geographic exposure expands as companies grow or restructure. A KYB profile captured at onboarding quickly becomes outdated and misleading if it is not refreshed. Relying on unchanged records creates false confidence, obscures emerging fraud patterns, and masks escalating money laundering or sanctions risk. Regulators consistently penalize institutions that treat KYB as a checkbox exercise rather than a living, continuously updated compliance control.
Core Components of Know Your Business (KYB)
Know Your Business (KYB) is built as a multi-layered compliance and risk intelligence framework designed to establish, validate, and continuously reaffirm the legitimacy of a business counterparty throughout its lifecycle. Unlike surface-level checks, KYB operates as a structural due diligence system that combines legal validation, ownership transparency, risk intelligence, and ongoing surveillance into a single operational discipline. Each component exists to eliminate a specific class of institutional risk—legal, financial, reputational, regulatory, and operational—while collectively enabling regulated entities to transact with confidence at scale. KYB is not a one-time onboarding ritual; it is a living control system embedded into onboarding, underwriting, payments, partnerships, and account management workflows.
At its core, KYB answers foundational questions that institutions cannot afford to leave ambiguous: Does this business legally exist? Who ultimately controls it? Is it connected to prohibited, sanctioned, or high-risk actors? How risky is it relative to the institution’s risk appetite? Does its risk profile remain stable over time? Each component below addresses one of these questions with depth, precision, and auditability. Together, they form a defensible compliance posture aligned with AML regulations, counter-terrorist financing rules, sanctions regimes, and global financial crime prevention standards. Skipping or weakening any single component breaks the KYB chain and exposes the institution to regulatory penalties, enforcement actions, correspondent banking risk, and severe reputational damage. The sections that follow break down each core KYB component in isolation, with equal operational weight and institutional importance.
Legal entity verification
Legal entity verification establishes whether a business exists as a recognized legal construct under applicable jurisdictional law and whether its foundational details are accurate, current, and internally consistent. This step anchors KYB in objective legal reality rather than self-asserted information. It involves validating primary identifiers and formation records directly against authoritative registries.
Key elements typically include:
- Registered legal name and any trading or DBA names
- Jurisdiction of incorporation and registration number
- Entity type (corporation, LLC, partnership, trust, foundation)
- Incorporation date and current legal status
- Registered address and principal place of business
Verification confirms the entity is active, lawfully formed, and not dissolved, struck off, or fraudulently represented. It also detects shell entities, impersonation attempts, and synthetic business identities. Without rigorous legal entity verification, all downstream KYB controls operate on an untrusted foundation.
Beneficial ownership identification
Beneficial ownership identification uncovers the natural persons who ultimately own, control, or exercise decisive influence over a business, regardless of complex corporate structures. This component is critical because financial crime risk almost always resides at the human level, not the entity name.
This process focuses on:
- Individuals meeting ownership thresholds (e.g., 10%, 25%, or jurisdiction-specific limits)
- Persons with significant control, voting rights, or decision authority
- Ownership chains spanning multiple entities and jurisdictions
- Trust settlors, trustees, protectors, and beneficiaries where applicable
Effective KYB requires tracing ownership through layers until real persons are identified, verified, and linked. Failure here enables anonymity, sanctions evasion, corruption, tax crimes, and laundering via corporate veils. Beneficial ownership transparency is the backbone of modern AML enforcement.
Sanctions, PEP, and adverse media screening
Sanctions, politically exposed person (PEP), and adverse media screening evaluates whether a business or its associated individuals are linked to prohibited, restricted, or high-risk activities. This component protects institutions from facilitating illegal or reputationally catastrophic relationships.
Screening typically covers:
- Global and local sanctions lists
- PEP databases across domestic and foreign jurisdictions
- Law enforcement watchlists and regulatory enforcement records
- Credible adverse media related to fraud, corruption, terrorism, or financial crime
Matches are risk-weighted, contextually analyzed, and dispositioned rather than blindly accepted. The objective is not exclusion by default, but informed decision-making. This layer directly safeguards against sanctions violations, regulatory fines, correspondent banking termination, and public trust erosion.
Risk assessment and classification
Risk assessment and classification translates KYB findings into an actionable risk profile that governs how a business is onboarded, monitored, and restricted. It synthesizes legal, ownership, geographic, industry, and behavioral risk signals into a structured decision framework.
Common risk factors include:
- Jurisdictional risk exposure
- Industry and business model risk
- Ownership complexity and transparency
- Transactional use cases and volume expectations
The outcome is a risk rating—low, medium, or high—that dictates enhanced due diligence requirements, approval thresholds, and monitoring intensity. Proper classification ensures resources are allocated proportionately and defensibly, aligning compliance rigor with actual risk.
Continuous monitoring and refresh
Continuous monitoring and refresh ensures KYB remains accurate as businesses evolve, ownership changes, and risk landscapes shift. Static KYB is operationally obsolete and regulatorily indefensible.
Ongoing controls include:
- Periodic data refresh and re-verification
- Real-time sanctions and adverse media monitoring
- Change detection in ownership, directors, or legal status
- Event-driven reviews triggered by risk signals
This component transforms KYB from a snapshot into a lifecycle control. It enables institutions to detect emerging risks early, maintain regulatory compliance, and respond proactively rather than reactively. Continuous monitoring closes the KYB loop and preserves long-term institutional integrity.
Know Your Business (KYB) vs Know Your Customer (KYC)
Know Your Business (KYB) and Know Your Customer (KYC) are frequently mentioned together, but they address fundamentally different risk surfaces, operate on different data structures, and fail in very different ways. KYC is designed to establish and continuously verify the identity, legitimacy, and risk posture of individual natural persons. KYB, by contrast, is designed to establish the legal existence, ownership reality, control structure, and operating legitimacy of business entities, which are inherently multi-layered, jurisdictionally fragmented, and structurally dynamic.
At a high level, KYC answers the question: “Who is this person, and can they lawfully participate in the financial system?”
KYB answers a far more complex question: “What exactly is this business, who truly owns and controls it, how does it operate, and what risks does it introduce into the financial ecosystem?”
KYB expands the compliance perimeter from a single identity to an entire corporate organism, including:
- Legal entity formation and registration status
- Beneficial ownership chains and ultimate controllers
- Directors, officers, and authorized signatories
- Jurisdictional exposure across incorporation, operations, and banking
- Ongoing changes in ownership, structure, and business activity
Unlike KYC, which is often front-loaded at onboarding, KYB is structurally continuous. Businesses evolve, restructure, acquire, dissolve, and pivot—meaning KYB must operate as a living control system, not a one-time verification event.
High-level comparison (KYB vs KYC)
| Dimension | KYC | KYB |
|---|---|---|
| Risk subject | Individual (natural person) | Legal entity (business, trust, partnership) |
| Identity structure | Single identity | Multi-layered ownership & control |
| Data sources | ID documents, biometrics, PEP/sanctions | Registries, UBO data, corporate filings, networks |
| Change frequency | Low to moderate | High and continuous |
| Failure impact | Localized | Systemic and network-amplified |
| Regulatory exposure | AML / CTF | AML / CTF / sanctions / tax / fraud / supply-chain |
The distinction is not semantic—it is structural, operational, and systemic.
Businesses vs individuals as risk subjects
Individuals and businesses represent fundamentally different classes of risk subjects, and treating them as equivalent is a category error that leads to compliance blind spots. An individual is a bounded entity: one legal identity, one set of documents, one behavioral profile. A business, however, is an abstract legal construct that exists through documents, relationships, delegated authority, and ownership layers.
Key differences in risk composition include:
- Multiplicity of actors
- Individuals act for themselves
- Businesses act through directors, officers, employees, agents, and intermediaries
- Opacity by design
- Individuals are expected to be transparent
- Businesses can legally obscure ownership through holding companies, trusts, and nominee structures
- Jurisdictional sprawl
- Individuals usually anchor to one or two jurisdictions
- Businesses routinely span multiple countries across incorporation, operations, banking, and taxation
- Delegated authority risk
- Individuals control their own actions
- Businesses delegate authority, increasing misuse and impersonation risk
From a compliance perspective, this means:
- KYC focuses on identity authenticity and behavioral consistency
- KYB focuses on entity legitimacy, control reality, and network exposure
A single business can embed the risk profiles of dozens—or hundreds—of individuals, making KYB a force multiplier for both risk and regulatory responsibility.
Structural differences in risk and failure modes
The way KYC fails and the way KYB fails are structurally different because the underlying systems they govern are different. KYC failures tend to be point failures; KYB failures tend to be network failures.
KYC failure modes typically include:
- Acceptance of forged or stolen identity documents
- Missed PEP or sanctions designation
- Inadequate ongoing monitoring of behavioral changes
- False negatives in transaction pattern analysis
These failures usually affect:
- One customer account
- A limited transaction set
- A narrow compliance remediation scope
KYB failure modes are broader and more destructive:
- Incorrect or missing beneficial ownership identification
- Failure to detect shell companies or front entities
- Inability to map complex ownership chains
- Outdated registry data masking control changes
- Undetected links to sanctioned or high-risk entities
Structurally, KYB failures propagate because:
- One business can control many accounts
- One entity can transact on behalf of many parties
- One shell structure can be reused across institutions
As a result, KYB failures do not stay isolated—they cascade across systems, counterparties, and jurisdictions, compounding regulatory and financial damage.
Why KYB failures are systemically more damaging
KYB failures are more damaging because businesses function as infrastructure nodes within the financial system. When an individual fails KYC, the risk is typically contained. When a business bypasses or defeats KYB controls, it gains the ability to move value, launder funds, evade sanctions, and finance illicit activity at scale.
Systemic damage arises from several compounding factors:
- Transaction amplification
- Businesses transact in higher volumes and values
- Illicit flows scale exponentially through corporate accounts
- Network embedding
- Businesses sit inside payment rails, supply chains, and correspondent networks
- One compromised entity contaminates multiple downstream partners
- Regulatory multiplier effect
- KYB failures trigger AML, sanctions, tax, and fraud violations simultaneously
- Penalties extend beyond fines to licensing, consent orders, and market exclusion
- Delayed detection
- Corporate structures change quietly and legally
- Ownership and control shifts often lag registry updates
- Reputational contagion
- Institutions linked to failed KYB cases face loss of trust from regulators, partners, and markets
In practical terms, KYB failures enable:
- Large-scale money laundering
- Sanctions evasion via layered entities
- Trade-based financial crime
- Abuse of fintech, payments, and banking infrastructure
This is why regulators increasingly view KYB not as an extension of KYC, but as a separate, higher-order control discipline—one that protects the financial system itself, not just individual institutions.
Who Needs Know Your Business (KYB) and When
Know Your Business (KYB) is required by any organization that establishes, maintains, or intermediates relationships with legal entities rather than individuals. KYB becomes mandatory at the precise moment an institution faces financial exposure, regulatory accountability, reputational risk, or systemic dependency on another business. This obligation is not discretionary; it is triggered by law, regulation, and supervisory expectation.
KYB is needed before onboarding, during periodic review, and whenever material changes occur in a business relationship. It applies across domestic and cross-border operations and intensifies with transaction volume, jurisdictional complexity, and ownership opacity.
KYB is essential when an organization must answer, with evidentiary certainty:
- Who owns and controls the business
- Whether the entity is legitimate, active, and lawfully registered
- Whether the business’s activities align with its declared purpose
- Whether the entity introduces AML, sanctions, fraud, or terrorist-financing risk
In short, KYB is required whenever trust must be engineered, not assumed.
Banks, fintechs, and financial infrastructure
Banks, fintech companies, and financial infrastructure providers are the primary and non-negotiable users of KYB, as they sit directly within regulated financial systems. Any institution that provides accounts, payments, lending, custody, or financial rails to businesses must apply KYB rigorously and continuously.
KYB is required across:
- Commercial banks onboarding corporate accounts and SMEs
- Digital banks and neobanks serving startups and online merchants
- Payment processors, acquiring banks, and PSPs
- Card networks, issuing platforms, and BIN sponsors
- Core banking, Banking-as-a-Service (BaaS), and embedded finance providers
These entities must verify:
- Legal existence and registration status
- Ultimate beneficial ownership (UBO) and control structures
- Nature of business activities and revenue sources
- Jurisdictional exposure and sanctions risk
For regulated financial actors, KYB is not a compliance function alone; it is a core risk-control mechanism underpinning AML, fraud prevention, and supervisory compliance.
Marketplaces and platforms
Marketplaces and digital platforms require KYB when they enable business-to-consumer or business-to-business economic activity at scale. Even when not licensed as financial institutions, these platforms increasingly fall under indirect regulatory scrutiny due to payment flows, merchant aggregation, and consumer exposure.
KYB is critical for platforms such as:
- E-commerce marketplaces onboarding third-party sellers
- Gig-economy and creator platforms paying businesses or studios
- SaaS platforms offering invoicing, payouts, or embedded payments
- App stores, advertising networks, and affiliate ecosystems
KYB allows platforms to:
- Prevent shell companies and fraudulent merchants
- Ensure sellers are legally registered and operational
- Detect prohibited or misrepresented business activities
- Reduce chargebacks, fraud, and downstream compliance risk
As regulators expand expectations around platform accountability, KYB has become essential to platform trust, marketplace integrity, and scalable growth, not merely a defensive compliance exercise.
High-risk and regulated industries
High-risk and heavily regulated industries face heightened KYB obligations due to their elevated exposure to financial crime, sanctions evasion, and regulatory enforcement. In these sectors, KYB depth, frequency, and documentation standards are materially higher.
Industries requiring advanced KYB include:
- Cryptocurrency, digital asset, and virtual asset service providers (VASPs)
- Gambling, gaming, and betting operators
- Money services businesses (MSBs) and remittance firms
- Forex, brokerage, and alternative investment platforms
- Defense, dual-use goods, and cross-border trade businesses
KYB in these contexts must address:
- Complex, multi-layered ownership structures
- Use of offshore entities and nominee arrangements
- Cross-border regulatory mismatches
- Enhanced sanctions, PEP, and adverse-media exposure
For high-risk sectors, KYB is not a one-time gate. It is an ongoing surveillance obligation essential to operational continuity, licensing retention, and regulatory survival.
Key Takeaways
Know Your Business (KYB) is a foundational compliance and risk-management framework that enables financial institutions, fintech companies, payment processors, and regulated platforms to establish who a business truly is, who controls it, and whether it can be trusted to operate within the financial system. The following takeaways capture the most essential, non-negotiable truths about KYB, distilled for absolute clarity and operational relevance.
- KYB is about business identity certainty, not paperwork
- It determines the legal existence, ownership structure, and control hierarchy of a business entity
- Document collection alone is insufficient without independent verification and cross-validation
- KYB exists to eliminate opacity in corporate structures
- Identifies Ultimate Beneficial Owners (UBOs) and controlling persons
- Prevents misuse of shell companies, front entities, and nominee directors
- KYB is a continuous process, not a one-time check
- Businesses can change ownership, directors, jurisdictions, and risk profiles over time
- Ongoing monitoring is critical to detect anomalies, sanctions exposure, or illicit behavior
- KYB is legally mandated across global regulatory regimes
- Required under AML, CTF, FATF guidance, and jurisdiction-specific financial regulations
- Non-compliance exposes institutions to fines, license revocation, and criminal liability
- KYB protects platforms from systemic financial crime
- Mitigates risks related to money laundering, terrorist financing, tax evasion, and fraud
- Acts as a first-line defense before transactions ever occur
- KYB directly impacts onboarding speed and business scalability
- Robust KYB frameworks reduce false positives and friction
- Automation and data-driven KYB enable compliant growth at scale
- KYB is inseparable from modern digital finance
- Essential for B2B payments, embedded finance, neobanking, crypto platforms, and marketplaces
- Serves as the trust layer that allows businesses to access financial infrastructure
In essence, KYB is the mechanism through which trust is engineered into business relationships, ensuring that only legitimate, transparent, and accountable entities are allowed to participate in regulated financial ecosystems.
Last Updated
December 23, 2025
Readers can explore more Fintech Explainers HERE.
Click HERE to explore more.
