One-sentence definition of Anti-Money Laundering (AML)
Anti-Money Laundering (AML) is the system-level legal, institutional, and operational framework designed to detect, prevent, disrupt, and report the movement and legitimization of illicit funds across financial systems over time.
What is Anti-Money Laundering (AML)
Anti-Money Laundering is a control system embedded into the fabric of modern finance, not an external regulatory accessory. It exists wherever money can be accepted, stored, transmitted, converted, invested, or withdrawn. This includes banks, payment processors, broker-dealers, insurance companies, money service businesses, fintech platforms, digital asset exchanges, custodians, and any intermediary that touches value.
At a structural level, AML is a behavioral interpretation framework. Financial systems process enormous volumes of legitimate transactions that, in isolation, often look identical to illicit ones. AML exists to distinguish lawful economic activity from criminal value movement by analyzing patterns, context, consistency, and plausibility rather than relying on single events.
AML treats money not as a static object, but as a flow with narrative meaning. Every sustained financial relationship implies a story: who the customer is, how they earn money, how they spend or move it, whom they transact with, and why those transactions make sense. AML evaluates whether observed financial behavior remains consistent with that story over time.
Crucially, AML operates under uncertainty. Financial institutions are not investigators with subpoena power, nor are they courts determining guilt. AML therefore functions using probabilistic judgment. Institutions are required to identify reasonable grounds for suspicion, not proof. This distinction defines AML’s entire architecture: thresholds, escalation paths, documentation standards, and reporting obligations.
AML is also continuous by necessity. Risk does not end at onboarding. Customers change jobs, businesses pivot, ownership structures evolve, geopolitical conditions shift, and criminal methods adapt. AML systems must therefore reassess risk dynamically, incorporating new data as relationships mature.
From an institutional standpoint, AML is a delegated public function. Governments outsource early detection of financial crime to private institutions by imposing legal obligations, audit expectations, and liability. In effect, AML turns financial institutions into frontline sensors in a global intelligence network.
AML is inseparable from operational design. Decisions about onboarding friction, transaction limits, product features, geographic reach, and growth strategy directly shape AML exposure. A system that allows instant global transfers with minimal friction necessarily carries higher laundering risk and must compensate with stronger AML controls.
In digital finance, AML increasingly functions as real-time decision logic. Faster settlement compresses the window for detection and intervention. This forces AML systems to evolve from retrospective review toward near-real-time interpretation, raising both technical and governance complexity.
At its deepest level, AML is about preserving the legitimacy of money itself. If money cannot be trusted as a lawful store and medium of value, financial systems cease to function. AML exists to protect that trust.
What Anti-Money Laundering (AML) is NOT
AML is not identity verification. Knowing a customer’s name, address, nationality, or legal existence does not explain economic behavior. Identity answers “who”; AML answers “why this money behaves this way.” A fully verified customer can still launder money if their financial activity lacks lawful explanation.
AML is not document sufficiency. Corporate charters, shareholder registers, and proof-of-address documents describe structure at a moment in time. Money laundering is dynamic. Documents without behavioral analysis create false confidence and frequently mask risk rather than mitigate it.
AML is not a transactional blacklist exercise. Screening against watchlists and adverse media flags known risks but does not detect unknown or emerging criminal activity. Most sophisticated laundering occurs below the threshold of obvious red flags.
AML is not synonymous with sanctions compliance. Sanctions enforce explicit prohibitions tied to geopolitical objectives. AML addresses criminal proceeds regardless of whether any sanctioned party or jurisdiction is involved. A transaction can be entirely sanctions-compliant and still be illicit.
AML is not fraud prevention. Fraud focuses on deception and victim loss. AML addresses the movement and legitimization of criminal value even when transactions are authorized, consensual, and victimless in appearance.
AML is not a one-time control. Passing onboarding checks, annual audits, or regulatory exams does not complete AML obligations. Many of the most severe AML enforcement actions involved institutions that were formally compliant but operationally ineffective.
AML is not technology ownership. Purchasing monitoring software does not equate to AML effectiveness. AML failures typically arise from poor calibration, weak governance, misaligned incentives, or inadequate escalation—none of which software alone can fix.
AML is not about eliminating risk. Financial systems cannot eliminate crime. AML manages risk by increasing detection probability, raising costs for criminals, and limiting scale. Zero-risk AML is neither achievable nor expected.
AML is not optional. It is mandatory public policy implemented through private infrastructure, enforced by criminal penalties, civil fines, license revocation, and market exclusion.
Related Announcements:
What Is Know Your Customer (KYC)? Definition, Process & Risks
What is Financial Technology (Fintech)? Definition, How It Works, Examples, Future
BX Partners Launches 12 Open-Architecture Portfolio Models on Nitrogen Partner Store to Deliver Risk…
TOPONE Markets Advances AI-Powered Analytical Tools and Deepens Service Presence in Vietnam to Stren…
KOHO Becomes a Payments Canada Member to Strengthen National Payments Access
Tokenization vs Securitization in Finance: Differences, Use Cases, Risks, and Future
Why AML exists
AML exists because crime scales through money.
Most criminal activity is economically constrained at small scale. What transforms crime into organized, transnational enterprise is the ability to convert illegal proceeds into reusable economic capital. Laundering removes friction, allowing profits to be reinvested, organizations to expand, and influence to be purchased.
Historically, law enforcement focused on arresting individuals and seizing assets after crimes occurred. This approach proved insufficient against networks that adapted faster than enforcement, operated across borders, and insulated leadership from direct exposure.
AML represents a strategic inversion: instead of chasing criminals everywhere, force money to betray them wherever it moves.
Financial systems are uniquely suited for this role because money leaves traces. Transactions generate records, timestamps, counterparties, currencies, jurisdictions, and behavioral patterns. AML exists to extract meaning from those traces before criminal proceeds fully integrate into the legitimate economy.
AML also exists to counter economic distortion. Illicit capital undermines fair competition by allowing criminal enterprises to undercut prices, absorb losses, and outbid legitimate actors. Over time, this distorts markets, inflates asset prices, and corrodes institutional integrity.
At a systemic level, unchecked money laundering threatens financial stability. It facilitates capital flight, weakens monetary controls, fuels corruption, and exposes economies to external shocks. AML therefore functions as a macroeconomic safeguard, not merely a crime-fighting tool.
Internationally, AML exists to enable financial interoperability. Cross-border banking depends on trust between jurisdictions. Without shared AML standards, correspondent relationships collapse, payment systems fragment, and capital controls proliferate. AML is the common language that allows global finance to function.
In the fintech era, AML exists to balance acceleration with control. Digital finance dramatically reduces friction: instant onboarding, real-time settlement, borderless access, programmable money. These same properties amplify abuse. AML provides the braking system that allows speed without systemic breakdown.
AML also exists because failure propagates. A single weak institution can become a laundering hub that contaminates entire networks. AML is therefore collective defense, not individual hygiene.
Finally, AML exists to preserve public trust. Financial systems rely on confidence that money represents lawful value. When that confidence erodes, participation declines, liquidity withdraws, and systems fracture. AML protects the social contract underlying modern finance.
How AML works (step-by-step)
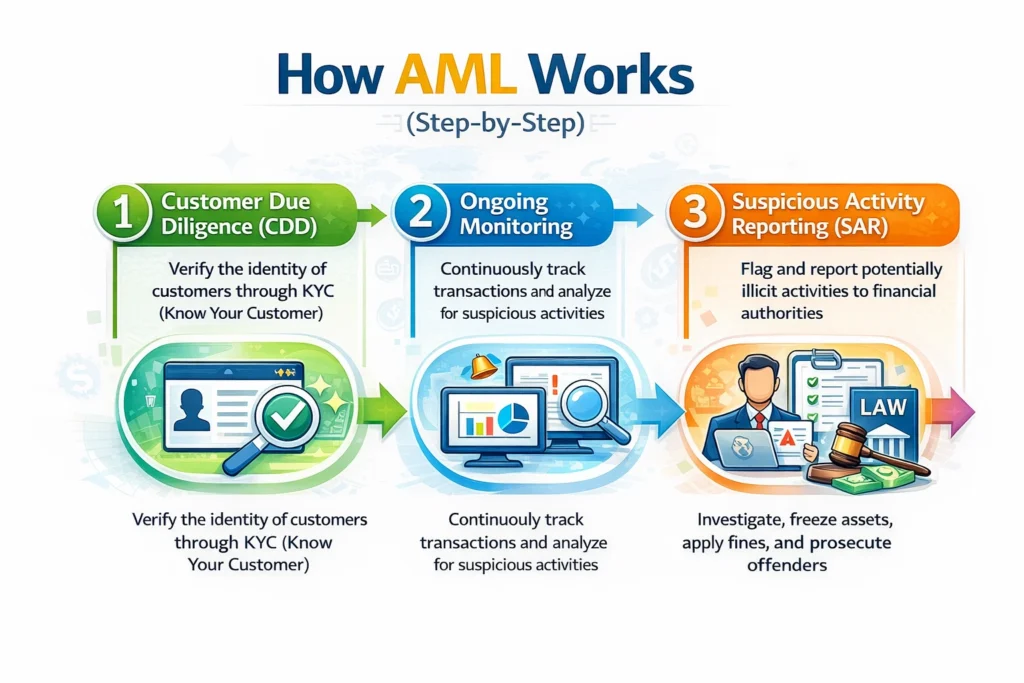
Anti-Money Laundering does not operate as a single linear process. It functions as a closed-loop control system that continuously ingests data, evaluates behavior, generates signals, applies human judgment, and feeds outcomes back into risk models. The steps below describe this lifecycle as it actually operates inside regulated institutions, not as simplified diagrams often present it.
Risk universe definition and exposure mapping
AML begins before any customer is onboarded or any transaction is processed, with the institution defining its risk universe. This step answers a foundational question: where can illicit value realistically enter or transit through this system?
Institutions map risk across multiple dimensions simultaneously:
- Customer types: individuals, SMEs, large corporates, trusts, charities, shell entities, financial intermediaries
- Products: deposit accounts, cards, wires, instant payments, trade finance, crypto on-ramps, custody
- Geographies: domestic vs cross-border, high-risk jurisdictions, offshore centers, sanctioned regions
- Channels: branch, online, mobile, API, correspondent relationships
- Transaction mechanics: cash-intensive flows, high-velocity micro-transactions, complex multi-leg transfers
This mapping is not descriptive; it is risk-weighted. Institutions assign relative exposure based on empirical data, regulatory guidance, typology reports, and historical enforcement actions. The output is a risk heatmap that dictates where AML controls must be strongest.
Without this step, AML becomes reactive and unfocused.
Customer onboarding and baseline risk construction
Once the risk universe is defined, AML systems construct a baseline risk profile for each customer at onboarding. This profile is not static classification; it is a hypothesis about expected behavior.
Baseline risk incorporates multiple vectors:
- Jurisdictional exposure
- Legal form and ownership complexity
- Business model or income source
- Anticipated transaction volume and frequency
- Expected counterparties, corridors, and instruments
Institutions often express baseline risk as a composite score derived from weighted variables:
Baseline Risk Score = Σ (Risk Factor_i × Weight_i)
Where:
- Risk Factor represents inherent exposure (e.g., country risk, industry risk)
- Weight reflects institutional risk appetite and regulatory sensitivity
The purpose is not to approve or reject in isolation, but to establish behavioral expectations. AML effectiveness depends on knowing what “normal” should look like for this specific customer.
Behavioral expectation modeling
AML systems then translate baseline risk into expected behavioral patterns. This is one of the most misunderstood steps.
Rather than asking “is this transaction suspicious?”, AML asks:
Is this transaction consistent with what we believe this customer should be doing?
Behavioral expectations may include:
- Average transaction size ranges
- Expected transaction frequency
- Typical counterparties or merchant categories
- Geographic corridors
- Cash vs non-cash usage
- Seasonality patterns
These expectations can be encoded through:
- Deterministic rules
- Statistical baselines
- Peer-group analysis
- Machine-learning clustering models
This step is essential because money laundering rarely appears abnormal in isolation. It appears abnormal only relative to context.
Transaction ingestion and normalization
Every transaction entering the system must be captured, standardized, and enriched before analysis. This is a foundational technical step often underestimated.
AML platforms normalize data across:
- Transaction amount and currency
- Timestamp and settlement mechanics
- Originating and beneficiary accounts
- Counterparty metadata
- Channel identifiers
- Instrument type
Normalization allows heterogeneous transactions—wires, card payments, crypto transfers—to be evaluated within a unified analytical framework.
Poor normalization leads to blind spots. AML failures frequently trace back to inconsistent data schemas rather than flawed detection logic.
Monitoring logic execution (rules, models, typologies)
Once normalized, transactions are evaluated through monitoring logic, which operates in parallel layers.
Deterministic rules
Rules capture known laundering behaviors, such as:
- Structuring below reporting thresholds
- Rapid movement through multiple accounts
- Circular or round-tripping transactions
- Sudden changes in velocity or volume
Rules are precise but brittle. They detect known patterns well but adapt poorly to novel behavior.
Statistical and peer-group models
Statistical models compare a customer’s activity against:
- Their own historical baseline
- Peer groups with similar profiles
This allows detection of relative anomalies, even when absolute thresholds are not breached.
Typology-based scenarios
Typologies encode documented laundering methods, such as trade-based laundering, mule networks, or crypto mixing behaviors. These scenarios are updated as criminal techniques evolve.
Modern AML systems often combine all three approaches to reduce both false positives and false negatives.
Alert generation and risk prioritization
When monitoring logic identifies deviations beyond tolerance thresholds, alerts are generated. Alerts are not equal; prioritization is critical.
Effective AML systems rank alerts using multi-factor scoring:
- Severity of deviation
- Customer baseline risk
- Regulatory exposure
- Potential downstream harm
Poor prioritization leads to analyst overload and missed high-risk cases. Many enforcement actions cite institutions for generating excessive low-value alerts while failing to escalate critical ones.
Human investigation and contextual judgment
Alerts escalate to human analysts, where AML transitions from automation to judgment.
Analysts assess:
- Plausibility of activity given customer profile
- Consistency across time
- Presence of corroborating indicators
- Quality of explanations or documentation
This step is intentionally human. Regulators expect institutions to apply reasoned judgment, not automated guilt assignment.
Analysts document rationale meticulously. The quality of documentation is as important as the decision itself, as it forms the basis for regulatory review.
Decisioning and escalation
Following investigation, institutions choose among several actions:
- Clear the alert with documented justification
- Request additional information from the customer
- Apply account restrictions or monitoring enhancements
- Terminate the relationship
- Escalate for regulatory reporting
This step embodies AML’s central principle: intervention before integration. The goal is not to prove crime, but to prevent the completion of laundering cycles.
Reporting and intelligence contribution
When suspicion reaches defined thresholds, institutions file mandatory reports with authorities. These reports serve two purposes:
- Fulfill legal obligations
- Contribute intelligence to broader enforcement efforts
Reports aggregate narrative explanation, transaction detail, and analytical reasoning. They do not assert guilt; they flag risk.
Continuous feedback and model recalibration
AML systems close the loop by feeding outcomes back into risk models:
- Cleared alerts refine thresholds
- Confirmed cases adjust typologies
- Regulatory feedback reshapes priorities
Without this feedback loop, AML degrades over time.
Related Announcements:
KOHO Becomes a Payments Canada Member to Strengthen National Payments Access
Sunflower Bank Launches Sunflower Insurance Solutions to Expand Wealth and Risk Management Services
Tokenized Deposits vs Stablecoins: Meaning, Differences, How They Work, Use Cases, Risks, Regulation…
Tokenization vs Cryptocurrency: Meaning, Differences, Regulation, and the Future of Finance
What Is SWIFT in Banking? The Global Financial Messaging Network Explained
BitGo Expands ETF Partnership With 21shares Across U.S. and EMEA to Support Global Crypto Staking an…
Key components of Anti-Money Laundering (AML)
AML effectiveness depends on interdependent components, not isolated tools.
Policy and governance framework
Defines risk appetite, escalation thresholds, accountability, and board oversight. Weak governance undermines all downstream controls.
Data infrastructure
Aggregates customer, transaction, counterparty, and external intelligence. Data completeness and accuracy directly determine detection quality.
Monitoring and analytics engine
Executes rules, models, and scenarios. This is the computational core of AML.
Case management and workflow
Manages investigations, documentation, quality assurance, and audit trails.
Human expertise
Trained analysts and compliance leaders who apply judgment, not checklists.
Oversight and assurance
Independent testing, audits, and regulatory engagement that validate effectiveness.
Real-world examples
Structuring through retail accounts
A customer deposits cash repeatedly just below reporting thresholds across multiple branches, followed by rapid electronic transfers. Individually benign deposits form a suspicious pattern when aggregated.
Trade-based money laundering
Over- or under-invoicing of goods to move value across borders disguised as legitimate trade payments.
Mule networks in digital payments
Large numbers of low-value transactions routed through newly opened accounts to obscure origin before consolidation.
Crypto layering
Funds move through exchanges, wallets, mixers, and bridges to obscure traceability before re-entry into fiat systems.
Use cases
AML applies across diverse financial contexts:
- Retail banking and payments
- Corporate and SME banking, including trade finance
- Correspondent banking and cross-border flows
- Fintech platforms with embedded finance
- Crypto exchanges, custodians, and on-ramps
- Insurance, securities, and asset management
Each use case requires tailored controls, but the underlying AML logic remains consistent.
Benefits
The benefits of Anti-Money Laundering are often misunderstood because they are systemic rather than transactional. AML does not primarily optimize revenue, speed, or user convenience. Its benefits accrue at the level of institutional resilience, market integrity, and long-term viability of financial systems.
Protection of financial system integrity
The most fundamental benefit of AML is that it preserves the legitimacy of financial infrastructure. Money functions as a social contract: participants accept it because they trust it represents lawful value. AML sustains that trust by ensuring financial systems do not become conduits for criminal proceeds.
When illicit capital enters financial systems unchecked, it contaminates pricing signals, distorts capital allocation, and erodes confidence. AML reduces this contamination by forcing criminal value to encounter friction, scrutiny, and exposure before it can integrate into the legitimate economy.
Disruption of criminal scalability
Crime becomes economically powerful only when profits can be laundered at scale. AML directly targets this scalability. By increasing detection probability, introducing delays, and creating points of failure, AML raises the operational cost of crime.
Criminal organizations adapt continuously, but each additional layer of AML control reduces efficiency and predictability. Even when laundering is not fully prevented, partial disruption reduces margins, increases error rates, and exposes networks to law enforcement over time.
Institutional risk containment
For financial institutions, AML acts as a risk firewall. Weak AML exposes institutions to regulatory penalties, license restrictions, correspondent banking termination, and reputational collapse. Strong AML contains these risks before they escalate.
This benefit is asymmetric. The cost of AML investment is finite and predictable. The cost of AML failure is potentially existential. From a risk management perspective, AML offers high downside protection.
Enablement of global financial access
AML is often framed as a barrier to inclusion, but at the system level it is the opposite. Shared AML standards enable cross-border trust. Without AML, international payments, correspondent banking, and global capital markets would fragment.
AML allows institutions in different jurisdictions to rely on each other’s controls. This interoperability is what enables global trade, remittances, and international investment at scale.
Regulatory defensibility and institutional credibility
AML provides institutions with defensible decision-making frameworks. When institutions can demonstrate structured risk assessment, documented judgment, and consistent escalation, regulators focus on improvement rather than punishment.
This credibility matters during examinations, enforcement inquiries, and crisis events. Institutions with mature AML programs retain regulatory trust even when isolated failures occur.
Strategic clarity in product design
AML forces institutions to explicitly confront risk trade-offs. Decisions about instant payments, anonymous instruments, high-risk geographies, or complex products cannot be made in abstraction. AML analysis clarifies which risks are acceptable, mitigable, or prohibitive.
Over time, this clarity improves product discipline and prevents uncontrolled risk accumulation.
Risks & limitations
Despite its benefits, AML is not a perfect system. It carries inherent limitations that cannot be eliminated, only managed.
Inherent uncertainty and false positives
AML operates under uncertainty. Suspicion is probabilistic, not factual. This inevitably produces false positives—legitimate customers flagged as suspicious.
False positives impose real costs: customer friction, analyst workload, delayed transactions, and reputational strain. No AML system can eliminate false positives without simultaneously increasing false negatives.
This trade-off is structural, not technical.
Adaptive adversaries
Criminal actors are not static. They observe enforcement actions, study public typologies, and rapidly adjust behavior. AML systems must therefore chase a moving target.
Static rules decay quickly. Even advanced models can be gamed once patterns are understood. AML is a perpetual arms race with no final victory state.
Data fragmentation and visibility gaps
No institution sees the full financial picture. Criminal networks exploit fragmentation by spreading activity across multiple institutions, jurisdictions, and instruments.
AML relies on partial visibility and delayed aggregation through regulatory reporting. This limits real-time detection of sophisticated cross-institution schemes.
Human dependency and inconsistency
AML ultimately depends on human judgment. Analysts interpret signals, assess plausibility, and document reasoning. Human judgment introduces variability, fatigue, bias, and error.
Scaling analyst quality is difficult. Training takes time, expertise is scarce, and turnover is high. Technology can assist but cannot fully replace judgment.
Regulatory asymmetry and over-compliance
AML regulations are often broad and principles-based. Institutions respond by over-complying to avoid penalties. This can lead to excessive de-risking, account closures, and exclusion of entire customer segments or geographies.
This risk is particularly acute for small businesses, migrants, charities, and emerging markets.
Cost–benefit imbalance at the margin
At extreme levels of control, incremental AML improvements deliver diminishing returns. Beyond a point, additional rules generate more noise than signal.
Determining where that point lies is difficult, especially under regulatory pressure. This leads to bloated systems that are expensive but not proportionally more effective.
Related Announcements:
GETCHOICE! Surpasses $5 Billion in Annual Utility Spend to Centralize Enterprise Utility Bill Pay an…
What Is Know Your Business (KYB)? Definition, Process & Compliance
Tokenization in Finance: Meaning, How It Works, Benefits, Risks and Regulation
What are Tokenized Deposits? Meaning, How They Work, Benefits, Risks and Global Adoption
What Is Atomic Settlement in Finance? Meaning, How It Works, Examples, Risks
Tokenization vs Cryptocurrency: Meaning, Differences, Regulation, and the Future of Finance
When AML makes sense / doesn’t
AML is mandatory in regulated finance, but its implementation intensity must be contextual.
When AML makes sense
AML delivers the highest value in environments where:
- Transaction volumes are large
- Cross-border flows are common
- Products are liquid and fungible
- Customers can operate at scale
- Value can be rapidly converted or layered
Banks, payment networks, correspondent institutions, crypto exchanges, and trade finance platforms fall squarely into this category.
AML also makes sense where trust externalities exist. Even if a single institution has low exposure, participation in shared networks requires compliance to protect collective integrity.
When AML reaches diminishing returns
AML becomes less effective when applied mechanically to:
- Low-value, closed-loop systems
- Single-purpose instruments with hard caps
- Environments with limited transferability
In such cases, excessive AML controls add friction without materially reducing risk. However, regulators often mandate minimum standards regardless of context.
When AML can cause harm
Poorly calibrated AML can:
- Exclude legitimate users
- Freeze funds without due process
- Disrupt humanitarian aid and NGOs
- Push activity into less regulated channels
These outcomes do not invalidate AML but highlight the need for risk-sensitive implementation, not blanket enforcement.
Cost & complexity
AML is one of the most expensive and complex control systems in modern finance.
Direct financial costs
AML costs include:
- Technology platforms and licenses
- Data infrastructure and storage
- Analyst staffing and training
- Independent audits and testing
- Regulatory engagement and remediation
For large institutions, AML budgets routinely run into hundreds of millions of dollars annually.
Operational complexity
AML systems span multiple teams: compliance, operations, engineering, data science, legal, risk, and audit. Coordination failures are common and costly.
Changes in regulation, typologies, or products cascade through systems, requiring continuous recalibration.
Opportunity cost
AML introduces friction into onboarding, transactions, and customer experience. This can reduce conversion rates, slow growth, and increase churn.
Institutions must constantly balance growth objectives against control requirements.
Complexity asymmetry
AML complexity scales non-linearly with size and scope. Global institutions face exponentially higher complexity than domestic players. Fintechs scaling rapidly often encounter AML strain precisely at the moment of growth inflection.
Long-term cost of failure
The most important cost consideration is failure cost. Enforcement actions routinely involve multi-billion-dollar fines, operational restrictions, and long-term reputational damage.
From a rational perspective, AML investment is not discretionary spending; it is insurance against catastrophic downside.
Regulatory perspective
Anti-Money Laundering is fundamentally a regulatory construct enforced through private infrastructure. While money laundering is a criminal offense prosecuted by the state, AML compliance is operationalized through mandatory obligations imposed on financial institutions. This design choice shapes every aspect of AML’s structure, enforcement, and evolution.
Delegated enforcement architecture
Governments do not directly monitor all financial transactions. Instead, they delegate early detection and reporting responsibilities to financial institutions, which are legally compelled to act as frontline monitors of financial behavior. Regulators define what must be detected, how suspicion is assessed, and when escalation is required, while institutions bear the operational burden.
This architecture rests on three pillars:
- Legal mandate: statutes defining money laundering offenses, reporting duties, and penalties
- Supervisory oversight: regulators examining whether institutions’ AML programs are effective
- Enforcement authority: power to impose fines, restrictions, or criminal liability
AML regulation is therefore less about prescribing exact methods and more about enforcing outcomes: institutions must demonstrate that their controls are reasonably designed to detect and report suspicious activity.
Principles-based regulation
Most AML regimes are principles-based, not rules-based. Regulators intentionally avoid specifying exact thresholds, models, or technologies. Instead, they require institutions to apply risk-based judgment.
This creates two consequences:
- Institutions retain flexibility to tailor AML programs to their risk profiles
- Institutions carry full accountability for failures, even when no explicit rule was violated
Principles-based regulation explains why AML enforcement actions often cite “failure to maintain effective controls” rather than violation of a specific technical rule.
Extraterritorial reach
AML regulation routinely has extraterritorial impact. Institutions operating globally are often subject to multiple overlapping AML regimes. Regulators assert jurisdiction based on factors such as:
- Currency cleared
- Correspondent relationships
- Market access
- Ownership or control
As a result, AML compliance is not confined to local law. Global institutions must harmonize controls to meet the most stringent applicable standard, not the weakest.
Enforcement philosophy
Modern AML enforcement emphasizes program effectiveness over intent. Regulators do not need to prove that an institution knowingly facilitated laundering. It is sufficient to show that controls were inadequate, poorly implemented, or ignored.
Common enforcement themes include:
- Weak governance and oversight
- Under-resourced compliance functions
- Poor model calibration
- Failure to act on known risks
- Repeated issues without remediation
AML penalties are designed to be deterrent, not proportional to transaction volume. This reflects the belief that AML failure threatens systemic trust.
Related Announcements:
What Is Know Your Business (KYB)? Definition, Process & Compliance
What Is ISO 20022? Meaning, How It Works, Benefits & Global Migration Timeline
Tokenization vs Cryptocurrency: Meaning, Differences, Regulation, and the Future of Finance
Tokenized Deposits vs Stablecoins: Meaning, Differences, How They Work, Use Cases, Risks, Regulation…
Strada Reports US Payroll Complexity Surge in 2025 Global Index
KOHO Becomes a Payments Canada Member to Strengthen National Payments Access
AML vs KYC
AML and Know Your Customer (KYC) are frequently conflated, but they serve distinct regulatory purposes.
KYC establishes customer identity and legitimacy at entry. AML evaluates financial behavior over time.
Key distinctions:
- KYC is front-loaded; AML is continuous
- KYC answers who; AML answers why and how
- KYC relies heavily on documents; AML relies on behavioral analysis
- KYC failure is often binary; AML risk is probabilistic
Regulators view KYC as a prerequisite for AML, not a substitute. A strong KYC program without effective AML monitoring is considered structurally deficient.
AML vs Fraud
AML and fraud controls intersect operationally but diverge in regulatory objective.
Fraud regulation focuses on consumer protection and loss prevention. AML regulation focuses on criminal proceeds and systemic risk.
Differences include:
- Fraud often involves unauthorized activity; AML often involves authorized transactions
- Fraud seeks restitution; AML seeks intelligence and prevention
- Fraud detection prioritizes speed; AML prioritizes documentation and escalation
Institutions that conflate fraud and AML frequently misallocate resources, over-optimize for customer reimbursement, and under-invest in long-term risk intelligence.
AML vs Sanctions
Sanctions compliance enforces explicit prohibitions imposed by governments. AML addresses implicit criminal risk.
Sanctions controls are deterministic: a match exists or does not. AML controls are interpretive: behavior may or may not indicate laundering.
Regulators treat sanctions breaches as violations of foreign policy. AML failures are treated as threats to financial integrity. Both carry severe penalties, but they operate on different logics.
Who should care
AML is often perceived as relevant only to compliance teams. In reality, its implications extend far beyond regulatory departments.
Financial institution boards and executives
Senior leadership is legally accountable for AML effectiveness. Regulators increasingly pursue personal liability, including fines and bans, where governance failures are evident.
Boards must understand AML not as operational noise but as enterprise risk.
Product and engineering teams
Design decisions directly affect AML exposure. API access, transaction speed, programmability, anonymity features, and geographic reach all shape laundering risk.
Ignoring AML during product design creates downstream remediation costs and regulatory conflict.
Fintech founders and operators
Rapid growth amplifies AML exposure faster than most other risks. Fintechs often encounter AML constraints precisely when scale accelerates.
AML maturity frequently determines whether a fintech can access banking partnerships, payment networks, or international markets.
Investors and counterparties
AML weaknesses represent hidden downside risk. Enforcement actions can destroy enterprise value overnight.
Sophisticated investors assess AML posture as part of due diligence, particularly in payments, crypto, and cross-border businesses.
Policymakers and regulators
AML effectiveness influences financial inclusion, capital mobility, and geopolitical leverage. Poorly calibrated AML regimes can exclude populations or drive activity underground.
Adoption timeline
AML did not emerge fully formed. Its evolution reflects changes in crime, finance, and globalization.
Early phase: criminalization of laundering
Initially, laundering itself was criminalized, focusing on prosecuting individuals after the fact.
Institutional phase: reporting obligations
Governments then imposed reporting duties on banks, recognizing that institutions were better positioned to observe flows.
Risk-based phase: proportional controls
As systems grew complex, regulators shifted to risk-based AML, allowing institutions to allocate resources based on exposure rather than uniform rules.
Digital phase: scale and speed challenges
Fintech, instant payments, and digital assets compressed timelines and expanded reach, forcing AML systems to evolve toward near-real-time monitoring.
Current phase: effectiveness and accountability
Today’s AML focus is on outcomes. Regulators evaluate whether systems actually detect risk, not merely whether policies exist.
Future outlook
AML is entering a period of structural tension driven by three forces: scale, complexity, and expectation.
Rising transaction velocity
Real-time payments and programmable money reduce detection windows. AML systems must operate faster without sacrificing judgment or defensibility.
Data and model governance pressure
As analytics grow more complex, regulators demand explainability. Black-box models face skepticism, particularly where decisions affect customer access.
Convergence with broader financial crime frameworks
AML is increasingly integrated with fraud, cybercrime, and sanctions intelligence. This convergence improves signal quality but raises governance complexity.
Inclusion and proportionality debates
Policymakers are under pressure to prevent AML from excluding vulnerable populations. Expect more scrutiny of de-risking and blanket controls.
Persistent asymmetry
No future AML system will eliminate laundering. The realistic objective remains containment, disruption, and intelligence, not eradication.
Related Announcements:
Tokenized Deposits vs CBDCs: Key Differences, Use Cases, Risks, and Future
Tokenization vs Digitization in Finance Explained
What Is Know Your Customer (KYC)? Definition, Process & Risks
ISX Financial EU PLC Appoints Andreas Artemiou as Chief Risk Officer to Strengthen Risk Governance
What is Financial Technology (Fintech)? Definition, How It Works, Examples, Future
What Is UBO Verification? What It Is, Process & Best Practices
Key takeaways
AML is a regulatory system enforced through private institutions, not a technical feature.
Its regulation is principles-based, outcome-oriented, and globally expansive.
AML differs fundamentally from KYC, fraud, and sanctions in purpose and method.
Responsibility for AML extends across leadership, product design, and strategy.
The future of AML will be shaped by speed, explainability, and proportionality—not by the promise of perfect detection.
Frequently Asked Questions on Anti-Money Laundering (AML)
What is AML and how does it work?
What AML is
Anti-Money Laundering (AML) is the system by which financial institutions detect, assess, disrupt, and report the movement of illicit funds so that criminal proceeds cannot be integrated into the legitimate financial system.
How AML works (in real terms, not theory)
AML works as a continuous control loop, not a one-time check:
Risk definition
Institutions first define where laundering risk exists (customer types, products, geographies, channels).
Customer risk profiling
Each customer is assigned an initial risk profile based on identity, jurisdiction, business model, ownership, and expected activity.
Behavioral monitoring
Transactions are continuously monitored to see whether actual behavior matches expected lawful behavior.
Anomaly detection
Deviations (velocity spikes, structuring, unusual counterparties, unexplained flows) prove suspicion, not guilt.
Human investigation
Analysts assess context, intent, and plausibility using judgment, not automation alone.
Escalation and reporting
If suspicion cannot be reasonably resolved, it is escalated and reported to authorities.
AML therefore works by interpreting economic behavior, not by verifying documents alone.
What are the 4 pillars of AML?
The four pillars of AML define what regulators expect every institution to have, regardless of size or technology stack.
1. Governance & internal controls
This includes:
AML policies and procedures
Clear accountability (board, senior management, compliance)
Defined risk appetite and escalation thresholds
Without governance, AML collapses regardless of tooling.
2. Risk assessment
Institutions must:
Identify inherent money-laundering risks
Assess customer, product, geographic, and transactional exposure
Update risk assessments regularly
AML is risk-based, not checklist-based.
3. Monitoring & reporting
This pillar covers:
Transaction monitoring systems
Alert investigation workflows
Timely suspicious activity reporting
This is where AML becomes operational.
4. Independent testing & training
Independent audits and model validation
Ongoing AML training for staff
Regulators treat lack of independent testing as a serious failure.
What are Anti-Money Laundering 3 types?
AML controls are commonly grouped into three functional types, based on when and how they operate.
1. Preventive AML
Controls designed to stop high-risk activity before it enters the system, such as:
Customer onboarding risk screening
Ownership transparency checks
Product and geography restrictions
This reduces exposure but cannot eliminate risk.
2. Detective AML
Controls designed to identify suspicious activity after it occurs, including:
Transaction monitoring
Behavioral analytics
Pattern recognition
This is the core of most AML programs.
3. Corrective AML
Controls applied after suspicion is confirmed, such as:
Account restrictions or exits
Regulatory reporting
Remediation and control enhancement
Corrective AML prevents recurrence and strengthens the system.
What is the main purpose of AML?
The main purpose of AML is to prevent criminal proceeds from entering, circulating within, or being legitimized by the financial system.
More precisely, AML exists to achieve four outcomes simultaneously:
Disrupt criminal economics
Crime only scales when profits can be reused. AML raises friction, increases detection risk, and reduces the usability of illicit funds.
Protect financial system integrity
Illicit capital distorts markets, corrupts competition, and undermines trust. AML preserves confidence in money as lawful value.
Create actionable financial intelligence
AML reporting aggregates fragmented transaction data across institutions, enabling authorities to detect organized and cross-border crime.
Shift enforcement upstream
Instead of reacting after crimes are complete, AML intervenes during the movement of money, before full integration occurs.
AML is therefore not about paperwork or compliance optics.
Its purpose is economic containment of crime.
Which is better, AML or KYC?
This is a false comparison.
AML and KYC are not alternatives — they are dependent layers.
Correct relationship
KYC is foundational
AML is operational
Why neither is “better”
KYC answers who the customer is
AML answers whether their financial behavior makes lawful sense over time
A system with strong KYC but weak AML will fail.
A system with AML but weak KYC cannot function.
Regulatory reality
Regulators explicitly treat:
KYC as a prerequisite
AML as the core obligation
In enforcement actions, failures are almost always cited as:
“Inadequate AML controls,”
not “insufficient KYC documents.”
So the correct answer is:
Neither is better. AML cannot exist without KYC, and KYC is useless without AML.
What is the main cause of AML?
AML exists because of one fundamental cause:
The scalability of crime through financial systems.
Breaking that down:
Primary cause
Criminal activity becomes economically powerful only when illicit proceeds can be laundered and reused.
Enabling factors that necessitate AML
Globalized banking and payments
Cross-border capital movement
Instant settlement and digital finance
Fragmented institutional visibility
Anonymous or pseudo-anonymous instruments
These conditions make it possible to:
Hide origin
Obscure ownership
Layer transactions
Integrate funds into the legitimate economy
AML is the systemic response to these conditions.
Without AML, modern financial systems would inevitably become crime-amplification engines.
What are the 4 stages of money laundering?
Money laundering is commonly described in four functional stages, which explain how illicit funds become usable without detection.
1. Placement:
This is the initial entry of illicit funds into the financial system.
Typical methods include:
Cash deposits (often structured below reporting thresholds)
Cash-intensive businesses
Conversion into monetary instruments
Crypto on-ramps
Risk characteristic: highest detection probability because funds are closest to the crime.
2. Layering:
This stage aims to obscure the origin and ownership of funds.
Common techniques:
Rapid transfers across multiple accounts
Cross-border movements
Use of shell companies and intermediaries
Trade-based manipulation (over/under-invoicing)
Crypto mixing and bridging
Risk characteristic: complexity increases, traceability decreases.
3. Integration:
Here, funds are reintroduced into the legitimate economy as apparently lawful wealth.
Examples:
Real estate purchases
Business investments
Loans to related entities
Luxury assets
Risk characteristic: funds appear legitimate and are hardest to distinguish from lawful capital.
4. Extraction / Enjoyment (modern extension):
In advanced laundering models, criminals then extract value for personal or organizational use.
This includes:
Lifestyle spending
Political influence
Further criminal reinvestment
Modern AML focuses on interrupting earlier stages, especially placement and layering.
What are the 4 elements of KYC?
KYC consists of four core elements, each serving a distinct compliance purpose.
1. Customer Identification:
Establishing:
Name
Date of birth/incorporation
Address
Official identification numbers
Answers: Who is the customer?
2. Customer Verification:
Validating identity through:
Government-issued documents
Digital identity systems
Independent data sources
Answers: Is this identity real and authentic?
3. Customer Due Diligence (CDD):
Understanding:
Nature of business or income
Expected transaction behavior
Ownership and control (for entities)
Answers: Does this customer make economic sense?
4. Ongoing Monitoring:
Ensuring:
Information remains current
Behavior aligns with expectations
Risk is reassessed over time
Answers: Does this customer remain consistent and lawful?
KYC is static at entry; AML makes it dynamic over time.
What is the first step of AML?
The first step of AML is institutional risk assessment, not KYC and not transaction monitoring.
Why this comes first
AML cannot function without first answering:
Where, how, and why could money laundering realistically occur in this institution?
Before any customer is onboarded, institutions must define their AML risk universe, covering:
Customer types (retail, SME, corporates, intermediaries)
Products (accounts, cards, wires, instant payments, crypto)
Geographies (domestic, cross-border, high-risk jurisdictions)
Channels (branch, online, API, correspondent banking)
Transaction mechanics (cash, velocity, fungibility)
This step determines:
Which customers require enhanced scrutiny
Which behaviors are “normal”
Where monitoring thresholds should sit
Regulatory reality:
Institutions repeatedly fail AML exams not because they missed alerts, but because they never defined risk properly at the start.
So the correct answer is:
AML begins with risk identification, not document collection.
What are the two types of money laundering?
At a structural level, money laundering occurs in two primary forms, regardless of method or instrument.
1. Cash-based money laundering:
This involves physical cash generated from crime being introduced into the financial system.
Typical characteristics:
High use of cash deposits
Structuring below reporting thresholds
Cash-intensive front businesses
Currency exchange abuse
Risk profile:
Highest risk at placement, easier to detect early, common in narcotics, corruption, and tax evasion.
2. Non-cash (or non-physical) money laundering:
This involves value laundering without physical cash, using digital or financial instruments.
Examples include:
Trade-based money laundering
Wire and correspondent banking abuse
Securities and derivatives layering
Crypto and digital asset laundering
Risk profile:
More complex, harder to detect, often cross-border, and dominant in large-scale organized crime.
Modern reality:
Most sophisticated laundering today is non-cash, because it scales faster and leaves fewer obvious traces.
How is AML prevented?
AML is not “prevented” by a single control. It is prevented through layered defense, where failure at one layer is caught by another.
Core AML prevention mechanisms
1. Risk-based customer controls
Customer risk scoring
Enhanced due diligence for high-risk profiles
Restrictions on products or geographies
Prevents high-risk exposure at entry.
2. Continuous transaction monitoring
Behavioral analysis
Pattern detection
Peer comparison
Detects laundering attempts during execution.
3. Human investigation and escalation
Analyst judgment
Contextual review
Reasoned decisioning
Prevents false clearance of suspicious activity.
4. Regulatory reporting and feedback
Suspicious activity reporting
Law enforcement intelligence
Control recalibration
Prevents repeat exploitation.
Critical truth
AML does not eliminate laundering.
It raises cost, increases detection probability, and reduces scalability.
That is prevention in economic terms.
What is the AML KYC process?
The AML–KYC process is a single continuous lifecycle, not two separate workflows. KYC establishes the starting truth; AML tests whether that truth remains valid over time.
Step-by-step AML–KYC lifecycle (how it actually works)
1. Customer Identification (KYC entry point)
The institution establishes:
Legal identity (individual or entity)
Ownership and control
Jurisdictional exposure
This answers: Who is entering the system?
2. Risk Profiling & Due Diligence (bridge between KYC and AML)
The institution evaluates:
Nature of business or income
Expected transaction behavior
Source of funds / source of wealth
Structural complexity
This answers: Does this customer make economic sense?
Risk level determines:
Standard Due Diligence (SDD)
Enhanced Due Diligence (EDD)
3. Behavioral Expectation Setting
Based on KYC + risk assessment, the institution defines:
Expected transaction size and frequency
Typical counterparties
Geographic corridors
Product usage patterns
This step is critical: AML cannot function without expectations.
4. Ongoing Transaction Monitoring (AML core)
Actual activity is continuously compared against expectations:
Deviations trigger alerts
Patterns matter more than single transactions
This answers: Is behavior consistent with lawful purpose?
5. Review, Escalation, and Reporting
When behavior cannot be reasonably explained:
Human investigation is performed
Suspicion is escalated
Regulatory reporting is filed if required
Key truth:
KYC is static validation.
AML is dynamic verification.
What are the early signs of AML?
Early AML warning signs are behavioral inconsistencies, not obvious crimes. Sophisticated laundering is subtle at the start.
High-value early indicators regulators care about
1. Mismatch between profile and activity
Examples:
Low-income profile with high transaction velocity
Dormant accounts becoming highly active
Small business showing corporate-scale flows
This is the single strongest early signal.
2. Unexplained transaction structuring
Repeated transactions just below thresholds
Artificial splitting of payments
Circular movement of funds
Indicates deliberate avoidance of detection.
3. Sudden behavioral shifts
New geographies without business rationale
New counterparties unrelated to stated purpose
Abrupt changes in transaction timing or frequency
AML systems treat change itself as risk.
4. Use of intermediaries without justification
Shell entities
Agents or third parties
Complex ownership with no commercial logic
Complexity without purpose is a red flag.
5. Resistance to transparency
Delayed responses to information requests
Inconsistent explanations
Refusal to provide supporting documentation
Legitimate customers explain behavior.
Launderers evade explanation.
Critical insight
AML does not wait for certainty.
Early signs trigger scrutiny, not accusation.
Who is responsible for AML?
AML responsibility is shared, layered, and legally enforceable.
1. Board of Directors & Senior Management
They carry ultimate accountability.
Regulators expect boards to:
Set AML risk appetite
Ensure adequate resources
Oversee effectiveness
Board ignorance is not a defense.
2. AML / Compliance Function
Responsible for:
Policy design
Monitoring frameworks
Investigations
Regulatory reporting
They execute AML but do not own all risk.
3. Business & Product Teams
They create risk through:
Customer acquisition
Product features
Geographic expansion
Regulators increasingly hold business teams accountable for AML failures caused by growth decisions.
4. Every Employee (collective responsibility)
Frontline staff, operations, and support teams are required to:
Recognize red flags
Escalate concerns
Follow AML procedures
AML failures often start with ignored internal warnings.
Final regulatory position
AML is not the compliance team’s problem alone.
It is an enterprise-wide obligation with personal liability at the top.
Sources:
Europol — Financial Intelligence & Money Laundering:
https://www.europol.europa.eu/crime-areas-and-statistics/crime-areas/economic-crime
Financial Action Task Force (FATF):
https://www.fatf-gafi.org/
World Bank — Financial Consumer Protection & AML:
https://www.worldbank.org/en/
Bank for International Settlements (BIS):
https://www.bis.org/
U.S. Financial Crimes Enforcement Network (FinCEN):
https://www.fincen.gov/what-we-do
Reserve Bank of India (RBI) — AML/KYC Guidelines:
https://www.rbi.org.in/Scripts/BS_ViewMasDirections.aspx?id=11566
Last Updated
December 22, 2025
Readers can explore more Fintech Explainers HERE.
Click HERE to explore more.
